- Messages
- 9,933
Damn Rambo, you're doing the lords work.
Follow along with the video below to see how to install our site as a web app on your home screen.
Note: This feature may not be available in some browsers.
This is an excellent op-ed from Glenn Greenwald in today's Guardian. This bears reading in full and I HIGHLY suggest you do so:
Foreign politicians and officials who took part in two G20 summit meetings in London in 2009 had their computers monitored and their phone calls intercepted on the instructions of their British government hosts, according to documents seen by the Guardian. Some delegates were tricked into using internet cafes which had been set up by British intelligence agencies to read their email traffic.
American spies based in the UK intercepted the top-secret communications of the then Russian president, Dmitry Medvedev, during his visit to Britain for the G20 summit in London, leaked documents reveal.
The details of the intercept were set out in a briefing prepared by the National Security Agency (NSA), America's biggest surveillance and eavesdropping organisation, and shared with high-ranking officials from Britain, Australia, Canada and New Zealand.
The document, leaked by the NSA whistleblower Edward Snowden and seen by the Guardian, shows the agency believed it might have discovered "a change in the way Russian leadership signals have been normally transmitted".
Snowden is online right now answering questions:
http://www.guardian.co.uk/world/2013/jun/17/edward-snowden-nsa-files-whistleblower
Yeah Harvey, she's an idiot. They should have asked her how she feels about the possibility of having her laptop camera turned on while she's boning someone or masturbating. LOL!



The surveillance of Americans' phone calls and Internet activity is "transparent," President Barack Obama said on television Monday… Read…
Want to know all the code names for America's massive intelligence gathering programs? Just browse through the "intelligence analysts" who post their resumes on the public career networking site LinkedIn. ANCHORY, NUCLEON, TRAFFICTHIEF, ARCMAP, SIGNAV, COASTLINE, DISHFIRE, FASTSCOPE, OCTAVE/CONTRAOCTAVE, PINWALE, UTT, WEBCANDID, FASCIA, OCTSKYWARD, INTELINK, METRICS, BANYAN, MARINA ... these all sound absolutely terrifying.
Of course, some of them are just mundane commercial software and systems. Finding the newly revealed NSA surveillance programs amidst the "risk management suites" is part of the fun.
American Civil Liberties Union techonologist Christopher Soghoian discovered that the secret programs the Washington Post revealed on June 15 can also be found by searching LinkedIn.
Linkedin profiles of people in Maryland that mention MARINA & NUCLEON have some fun other codenames like TRAFFICTHIEF http://t.co/7DQ5uaJ1BPThe profile linked by the ACLU's Soghoian lists more than two dozen intelligence programs with menacing names in the current techno-creep NSA style. This analyst also says he is responsible for NSA PowerPoint presentations to explain the massive surveillance systems to intelligence management and political leaders: "Prepared topic-specific, detailed presentations for senior leadership using Powerpoint, Word, ZapGrab, ARCMap, and SIGNAV."
— Christopher Soghoian (@csoghoian) June 16, 2013
Front located many similar lists of current NSA projects on other career and networking sites, including this one on Indeed.com:
Tools Used: Cadence/UTT, Blazing Saddles, Xkeyscore, Marina, Maui/Anchory, Sharkfinn, Agility, Mastershake, Pinwale, UIS, TKB, Target Profiler, Agent Logic, NKB/Foxtrail, Banyan, Bellview, Octskyward, Cineplex, Arcmap, Analyst Notebook/Renoir, Microsft Powerpoint, /Excel, NSLOOKUP, Traceroutes, Whois, Treasuremap, Goldpoint, Nucleon, Octskyward, Goldminer, Roadbed, RT-RG Tool Suite, Tuningfork, Pathfinder, Cloud_ABR, AirgapIn fact, the names of these programs are all over the Internet, including lengthy descriptions of the technology and methodology included within working papers and presentations intended for NSA management. Familiar with "BROOMSTICK"? There are many Top Secret-clearance jobs available!
Here's the introduction to something called "TEMPEST 101":
When modern electrical devices operate they generate electromagnetic fields. Digital computers, radio equipment, typewriters, and so on generate massive amounts of electromagnetic signals which if properly intercepted and processed will allow certain amounts of information to be reconstructed based on these "compromising emanations". Basically anything with a microchip, diode, or transistor, gives off these fields.Relax! Or don't. It doesn't really matter. They can see, hear and read whatever you're seeing, hearing, reading or typing.
Compromising emanations are these unintentional intelligence-bearing signals, which, if intercepted and analyzed, potentially disclose the national security information, transmitted, received, handled, or otherwise processed by any information-processing equipment.
These compromising emanation signals can then escape out of a controlled area by power line conduction, other fortuitous conduction paths such as the air conditioning duct work, or by simply radiating a signal into the air (like a radio station).
An excellent example of these compromising emanations may be found in modems and fax machines which utilize the Rockwell DataPump modem chip sets and several modems made by U.S. Robotics. When these modems operate they generate a very strong electromagnetic field which may be intercepted, demodulated, and monitored with most VHF radios. This is also a very serious problem with many speaker phone systems used in executive conference rooms.
This is also a very serious problem with many fax machines, computer monitors, external disc drives, CD-R drives, scanners, printers, and other high bandwidth or high speed peripherals.
If an eavesdropper is using high quality intercept equipment the signal may be easily acquired several hundred feet or more away from the target.
Finally, here's a detailed profile of NSA surveillance programs from Booz Allen Hamilton—Edward Snowden's former employer:
BoozAllenHamiltonNSA (PDF)
BoozAllenHamiltonNSA (Text)
12.43pm ET
Final question from Glenn Greenwald:
Anything else you’d like to add?
Answer:
Thanks to everyone for their support, and remember that just because you are not the target of a surveillance program does not make it okay. The US Person / foreigner distinction is not a reasonable substitute for individualized suspicion, and is only applied to improve support for the program. This is the precise reason that NSA provides Congress with a special immunity to its surveillance.12.41pm ET
Question:
So far are things going the way you thought they would regarding a public debate? – tikkamasala
Answer:
Initially I was very encouraged. Unfortunately, the mainstream media now seems far more interested in what I said when I was 17 or what my girlfriend looks like rather than, say, the largest program of suspicionless surveillance in human history.12.37pm ET
Follow-up from the Guardian's Spencer Ackerman:
Regarding whether you have secretly given classified information to the Chinese government, some are saying you didn't answer clearly - can you give a flat no?
Answer:
No. I have had no contact with the Chinese government. Just like with the Guardian and the Washington Post, I only work with journalists.12.34pm ET
Question:

AhBrightWings
17 June 2013 2:12pm
My question: given the enormity of what you are facing now in terms of repercussions, can you describe the exact moment when you knew you absolutely were going to do this, no matter the fallout, and what it now feels like to be living in a post-revelation world? Or was it a series of moments that culminated in action? I think it might help other people contemplating becoming whistleblowers if they knew what the ah-ha moment was like. Again, thanks for your courage and heroism.
Answer:
I imagine everyone's experience is different, but for me, there was no single moment. It was seeing a continuing litany of lies from senior officials to Congress - and therefore the American people - and the realization that that Congress, specifically the Gang of Eight, wholly supported the lies that compelled me to act. Seeing someone in the position of James Clapper - the Director of National Intelligence - baldly lying to the public without repercussion is the evidence of a subverted democracy. The consent of the governed is not consent if it is not informed.12.28pm ET
Question:

Ryan Latvaitis
17 June 2013 2:34pm
What would you say to others who are in a position to leak classified information that could improve public understanding of the intelligence apparatus of the USA and its effect on civil liberties?
What evidence do you have that refutes the assertion that the NSA is unable to listen to the content of telephone calls without an explicit and defined court order from FISC?
Answer:
This country is worth dying for.12.24pm ET
Question:
Do you believe that the treatment of Binney, Drake and others influenced your path? Do you feel the "system works" so to speak? #AskSnowdenAnswer:
— Jacob Appelbaum (@ioerror) June 17, 2013
Binney, Drake, Kiriakou, and Manning are all examples of how overly-harsh responses to public-interest whistle-blowing only escalate the scale, scope, and skill involved in future disclosures. Citizens with a conscience are not going to ignore wrong-doing simply because they'll be destroyed for it: the conscience forbids it. Instead, these draconian responses simply build better whistleblowers. If the Obama administration responds with an even harsher hand against me, they can be assured that they'll soon find themselves facing an equally harsh public response.12.12pm ET
This disclosure provides Obama an opportunity to appeal for a return to sanity, constitutional policy, and the rule of law rather than men. He still has plenty of time to go down in history as the President who looked into the abyss and stepped back, rather than leaping forward into it. I would advise he personally call for a special committee to review these interception programs, repudiate the dangerous "State Secrets" privilege, and, upon preparing to leave office, begin a tradition for all Presidents forthwith to demonstrate their respect for the law by appointing a special investigator to review the policies of their years in office for any wrongdoing. There can be no faith in government if our highest offices are excused from scrutiny - they should be setting the example of transparency.
Question:

Mathius1
17 June 2013 2:54pm
Is encrypting my email any good at defeating the NSA survelielance? Id my data protected by standard encryption?
Answer:
Encryption works. Properly implemented strong crypto systems are one of the few things that you can rely on. Unfortunately, endpoint security is so terrifically weak that NSA can frequently find ways around it.12.10pm ET
Question:
US officials say terrorists already altering TTPs because of your leaks, & calling you traitor. Respond? http://t.co/WlK2qpYJki #AskSnowdenAnswer:
— Kimberly Dozier (@KimberlyDozier) June 17, 2013
US officials say this every time there's a public discussion that could limit their authority. US officials also provide misleading or directly false assertions about the value of these programs, as they did just recently with the Zazi case, which court documents clearly show was not unveiled by PRISM.Updated at 12.11pm ET
Journalists should ask a specific question: since these programs began operation shortly after September 11th, how many terrorist attacks were prevented SOLELY by information derived from this suspicionless surveillance that could not be gained via any other source? Then ask how many individual communications were ingested to acheive that, and ask yourself if it was worth it. Bathtub falls and police officers kill more Americans than terrorism, yet we've been asked to sacrifice our most sacred rights for fear of falling victim to it.
Further, it's important to bear in mind I'm being called a traitor by men like former Vice President Dick Cheney. This is a man who gave us the warrantless wiretapping scheme as a kind of atrocity warm-up on the way to deceitfully engineering a conflict that has killed over 4,400 and maimed nearly 32,000 Americans, as well as leaving over 100,000 Iraqis dead. Being called a traitor by Dick Cheney is the highest honor you can give an American, and the more panicked talk we hear from people like him, Feinstein, and King, the better off we all are. If they had taught a class on how to be the kind of citizen Dick Cheney worries about, I would have finished high school.
12.04pm ET
Question:
Guardian staff
Spencer Ackerman
17 June 2013 4:16pm
Edward, there is rampant speculation, outpacing facts, that you have or will provide classified US information to the Chinese or other governments in exchange for asylum. Have/will you?
Answer:
This is a predictable smear that I anticipated before going public, as the US media has a knee-jerk "RED CHINA!" reaction to anything involving HK or the PRC, and is intended to distract from the issue of US government misconduct. Ask yourself: if I were a Chinese spy, why wouldn't I have flown directly into Beijing? I could be living in a palace petting a phoenix by now.11.55am ET
Question:

MonaHol
17 June 2013 4:37pm
Ed Snowden, I thank you for your brave service to our country.
Some skepticism exists about certain of your claims, including this:
I, sitting at my desk, certainly had the authorities to wiretap anyone, from you, or your accountant, to a federal judge, to even the President if I had a personal email.Do you stand by that, and if so, could you elaborate?
Answer:
Yes, I stand by it. US Persons do enjoy limited policy protections (and again, it's important to understand that policy protection is no protection - policy is a one-way ratchet that only loosens) and one very weak technical protection - a near-the-front-end filter at our ingestion points. The filter is constantly out of date, is set at what is euphemistically referred to as the "widest allowable aperture," and can be stripped out at any time. Even with the filter, US comms get ingested, and even more so as soon as they leave the border. Your protected communications shouldn't stop being protected communications just because of the IP they're tagged with.11.41am ET
More fundamentally, the "US Persons" protection in general is a distraction from the power and danger of this system. Suspicionless surveillance does not become okay simply because it's only victimizing 95% of the world instead of 100%. Our founders did not write that "We hold these Truths to be self-evident, that all US Persons are created equal."
Question:

HaraldK
17 June 2013 2:45pm
What are your thoughts on Google's and Facebook's denials? Do you think that they're honestly in the dark about PRISM, or do you think they're compelled to lie?
Perhaps this is a better question to a lawyer like Greenwald, but: If you're presented with a secret order that you're forbidding to reveal the existence of, what will they actually do if you simply refuse to comply (without revealing the order)?
Answer:
Their denials went through several revisions as it become more and more clear they were misleading and included identical, specific language across companies. As a result of these disclosures and the clout of these companies, we're finally beginning to see more transparency and better details about these programs for the first time since their inception.11.40am ET
They are legally compelled to comply and maintain their silence in regard to specifics of the program, but that does not comply them from ethical obligation. If for example Facebook, Google, Microsoft, and Apple refused to provide this cooperation with the Intelligence Community, what do you think the government would do? Shut them down?

Anthony De Rosa
17 June 2013 2:18pm
1) Define in as much detail as you can what "direct access" means.
2) Can analysts listen to content of domestic calls without a warrant?
2) NSA likes to use "domestic" as a weasel word here for a number of reasons. The reality is that due to the FISA Amendments Act and its section 702 authorities, Americans’ communications are collected and viewed on a daily basis on the certification of an analyst rather than a warrant. They excuse this as "incidental" collection, but at the end of the day, someone at NSA still has the content of your communications. Even in the event of "warranted" intercept, it's important to understand the intelligence community doesn't always deal with what you would consider a "real" warrant like a Police department would have to, the "warrant" is more of a templated form they fill out and send to a reliable judge with a rubber stamp.Glenn Greenwald follow up: When you say "someone at NSA still has the content of your communications" - what do you mean? Do you mean they have a record of it, or the actual content?
Both. If I target for example an email address, for example under FAA 702, and that email address sent something to you, Joe America, the analyst gets it. All of it. IPs, raw data, content, headers, attachments, everything. And it gets saved for a very long time - and can be extended further with waivers rather than warrants.11.27am ET
Question:

Anthony De Rosa
17 June 2013 2:18pm
1) Define in as much detail as you can what "direct access" means.
2) Can analysts listen to content of domestic calls without a warrant?
Answer:
1) More detail on how direct NSA's accesses are is coming, but in general, the reality is this: if an NSA, FBI, CIA, DIA, etc analyst has access to query raw SIGINT databases, they can enter and get results for anything they want. Phone number, email, user id, cell phone handset id (IMEI), and so on - it's all the same. The restrictions against this are policy based, not technically based, and can change at any time. Additionally, audits are cursory, incomplete, and easily fooled by fake justifications. For at least GCHQ, the number of audited queries is only 5% of those performed.Updated at 11.41am ET
11.23am ET
Question:

Gabrielaweb
17 June 2013 2:17pm
Why did you wait to release the documents if you said you wanted to tell the world about the NSA programs since before Obama became president?
Answer:
Obama's campaign promises and election gave me faith that he would lead us toward fixing the problems he outlined in his quest for votes. Many Americans felt similarly. Unfortunately, shortly after assuming power, he closed the door on investigating systemic violations of law, deepened and expanded several abusive programs, and refused to spend the political capital to end the kind of human rights violations like we see in Guantanamo, where men still sit without charge.11.20am ET
Question:

D. Aram Mushegian II
17 June 2013 2:16pm
Did you lie about your salary? What is the issue there? Why did you tell Glenn Greenwald that your salary was $200,000 a year, when it was only $122,000 (according to the firm that fired you.)
Answer:
I was debriefed by Glenn and his peers over a number of days, and not all of those conversations were recorded. The statement I made about earnings was that $200,000 was my "career high" salary. I had to take pay cuts in the course of pursuing specific work. Booz was not the most I've been paid.11.17am ET
Question:

ActivistGal
17 June 2013 2:15pm
You have said HERE that you admire both Ellsberg and Manning, but have argued that there is one important distinction between yourself and the army private...
"I carefully evaluated every single document I disclosed to ensure that each was legitimately in the public interest," he said. "There are all sorts of documents that would have made a big impact that I didn't turn over, because harming people isn't my goal. Transparency is."Are you suggesting that Manning indiscriminately dumped secrets into the hands of Wikileaks and that he intended to harm people?
Answer:
No, I'm not. Wikileaks is a legitimate journalistic outlet and they carefully redacted all of their releases in accordance with a judgment of public interest. The unredacted release of cables was due to the failure of a partner journalist to control a passphrase. However, I understand that many media outlets used the argument that "documents were dumped" to smear Manning, and want to make it clear that it is not a valid assertion here.11.13am ET
Question:
Guardian staff
ewenmacaskill
17 June 2013 3:07pm
I should have asked you this when I saw you but never got round to it........Why did you just not fly direct to Iceland if that is your preferred country for asylum?
Answer:
Leaving the US was an incredible risk, as NSA employees must declare their foreign travel 30 days in advance and are monitored. There was a distinct possibility I would be interdicted en route, so I had to travel with no advance booking to a country with the cultural and legal framework to allow me to work without being immediately detained. Hong Kong provided that. Iceland could be pushed harder, quicker, before the public could have a chance to make their feelings known, and I would not put that past the current US administration.11.07am ET
Question:
Guardian staff
GlennGreenwald
17 June 2013 2:11pm
Let's begin with these:
1) Why did you choose Hong Kong to go to and then tell them about US hacking on their research facilities and universities?
2) How many sets of the documents you disclosed did you make, and how many different people have them? If anything happens to you, do they still exist?
Answer:
1) First, the US Government, just as they did with other whistleblowers, immediately and predictably destroyed any possibility of a fair trial at home, openly declaring me guilty of treason and that the disclosure of secret, criminal, and even unconstitutional acts is an unforgivable crime. That's not justice, and it would be foolish to volunteer yourself to it if you can do more good outside of prison than in it.
Second, let's be clear: I did not reveal any US operations against legitimate military targets. I pointed out where the NSA has hacked civilian infrastructure such as universities, hospitals, and private businesses because it is dangerous. These nakedly, aggressively criminal acts are wrong no matter the target. Not only that, when NSA makes a technical mistake during an exploitation operation, critical systems crash. Congress hasn't declared war on the countries - the majority of them are our allies - but without asking for public permission, NSA is running network operations against them that affect millions of innocent people. And for what? So we can have secret access to a computer in a country we're not even fighting? So we can potentially reveal a potential terrorist with the potential to kill fewer Americans than our own Police? No, the public needs to know the kinds of things a government does in its name, or the "consent of the governed" is meaningless.
2) All I can say right now is the US Government is not going to be able to cover this up by jailing or murdering me. Truth is coming, and it cannot be stopped.
Obama: Secret Court System for NSA Spying Is "Transparent"
The FISA court system, the proceedings of which are closed to the public and the records of which are classified, is "transparent," President Obama told Charlie Rose in an interview broadcast on PBS last night:
It is transparent. That's why we set up the FISA court. Look, the whole point of my concern, before I was president—because some people say, 'Well, you know, Obama was this raving liberal before. Now he's, you know, Dick Cheney.' Dick Cheney sometimes says, 'Yeah, you know? He took it all lock, stock, and barrel.'"Transparent" in this case seems to mean "overseen in some way by all three branches of the federal government." Which is something, certainly, even if FISA warrant requests are almost never denied by the courts, but I'm not sure it counts as "transparent."
My concern has always been not that we shouldn't do intelligence gathering to prevent terrorism, but rather are we setting up a system of checks and balances? So, on this telephone program, you've got a federal court with independent federal judges overseeing the entire program. And you've got Congress overseeing the program, not just the intelligence committee and not just the judiciary committee—but all of Congress had available to it before the last reauthorization exactly how this program works.
Obama and Rose also discussed Syria, which the president correctly noted "is not Iraq."
‘Tis of thee
I want to comment on this widely discussed bit by Josh Marshall:
Let me put my cards on the table. At the end of the day, for all its faults, the US military is the armed force of a political community I identify with and a government I support. I’m not a bystander to it. I’m implicated in what it does and I feel I have a responsibility and a right to a say, albeit just a minuscule one, in what it does. I think a military force requires a substantial amount of secrecy to operate in any reasonable way. So when someone on the inside breaks those rules, I need to see a really, really good reason. And even then I’m not sure that means you get off scott free. It may just mean you did the right thing.I, like Josh Marshall, identify very strongly with the political community called the United States of America. But for precisely that reason, my reaction is almost precisely the opposite of Marshall’s.
So do I see someone [Manning] who takes an oath and puts on the uniform and then betrays that oath for no really good reason as a hero? No.
The Snowden case is less clear to me. At least to date, the revelations seem more surgical. And the public definitely has an interest in knowing just how we’re using surveillance technology and how we’re balancing risks versus privacy. The best critique of my whole position that I can think of is that I think debating the way we balance privacy and security is a good thing and I’m saying I’m against what is arguably the best way to trigger one of those debates.
But it’s more than that. Snowden is doing more than triggering a debate. I think it’s clear he’s trying to upend, damage — choose your verb — the US intelligence apparatus and policies he opposes. The fact that what he’s doing is against the law speaks for itself. I don’t think anyone doubts that narrow point. But he’s not just opening the thing up for debate. He’s taking it upon himself to make certain things no longer possible, or much harder to do. To me that’s a betrayal. I think it’s easy to exaggerate how much damage these disclosures cause. But I don’t buy that there are no consequences. And it goes to the point I was making in an earlier post. Who gets to decide? The totality of the officeholders who’ve been elected democratically – for better or worse – to make these decisions? Or Edward Snowden, some young guy I’ve never heard of before who espouses a political philosophy I don’t agree with and is now seeking refuge abroad for breaking the law?
As a human being, it is very important to me to be good. But I am not meaningfully a human being as an individual. No one is, no matter how libertarian ones philosophy or how sterilely individualistic ones economic models. I do not identify with the political community called the United States like I might identify with a football team, hoping for victory against rivals simply because it is mine, my team. I identify with the United States of America as a vast and complex social and moral agent of which I have the privilege to be a part. I am elevated by my affiliation with, incorporation within, that community when it is a good community. I am diminished and pained and made nauseous when it is an evil community. Of course it is both, always, in various degrees, in my own shifting perceptions and those of others and in whatever unknowable objective reality might ever be ascribed to such a thing. But there are preponderances. A decade ago, my view was that the United States was, on the whole, in this imperfect realm of man, a good community. “The arc of the moral universe is long, but it bends towards justice, ” said Dr. King. I believed that about the United States, and I believed that about the United States’ role in the larger world. Now I hear various smug, self-righteous, powerful figures intone those words and I want to puke. In my tiny, flawed view — but I don’t think I am alone in this — the preponderances have shifted. As a community, our flaws are eclipsing our virtues. Men and women are imperfect, human communities are imperfect, but there are differences of degree and they matter. We are all born sinners, avaricious machines, selfish genes, but some work and strive and, to various degrees, perhaps even succeed at being better than they might be, and we should notice that, honor it. And when we are small and mean — perhaps without bad intentions but life is hard and the world is complex and we are buffeted by so many different forces, so many “incentives” — when we notice that we are small and mean, we should dishonor that, and work to change it.
In the 1980s, Ronald Reagan referred to the Soviet Union as an evil empire, and he was right to do so. That never meant that Russian people, individually, were bad people. That did not and would not justify anyone’s blowing up a Moscow apartment building, or attacking their soldiers, or any other prima facie awful thing. Violence in the service of good is not an impossible thing, perhaps, but it is a rare and very delicate thing at best. Violence ought never be justified in broad, sloppy brush strokes. Nothing would have justified a terrorist act against the Soviet Union, but it was a community whose moral character, with respect to both the lived experience inside it and its influence externally, was malign, and it was a matter of serious concern to people within and without that it should change. The community that was the Soviet Union is still evolving, and the jury is still out, as it will ever be, because human affairs are never permanent. For the sake of the people inside that community and for the sake of all the rest of us, we ought to wish them the best.
It pains me very much to say so, but the United States today is not a benign community. We have, over the last decade, undermined nearly all of the reasons that I, perhaps as a fool, thought distinguished us as virtuous, in our own particular way, despite our many flaws. A decade ago, I trusted our institutions, our government, our think tanks and university and third estate, our processes and our evaluations of our own competences, and supported what turned out to be a disastrous war in Iraq. Even though I observed what at the time were pretty obvious housing and credit bubbles, I believed our system was self-correcting, that those who fueled those errors would eventually be held accountable, economically and sometimes criminally, that we would suffer institutions to fall and titans to be shamed in order to preserve the integrity of our economy. I remember how ashamed I was when, in 2005, my then-girlfriend (now wife) came to visit the United States, and we were driving around with people on NPR debating whether torture was OK. Today my country holds people it has exonerated of wrongdoing in a tropical prison for indefinite terms because it cannot overcome the bureaucratic and political obstacles to letting them live, somewhere, the lives that they like each of us have been blessed with. Today my country sends remote control airplanes into a country we are not at war with and kills people it cannot identify in a program it assures us is “surgical”. When called to account for harm to noncombatants, it classifies “males of military age” as militants to keep the statistics flattering.
I am, and I will always be, a member of the political community called the United States of America. That is why these things pain me. The fact that I identify with this community does not mean I identify with the state, its government, its military institutions, even its civil society as presently constituted. I certainly want to identify with those things. I certainly used to identify with those things, ostentatiously and very proudly. In the community we all wish we belonged to, we would honor the state and the constellation of prominent institutions that surround it, banks and universities and newsmedia, as constituting a system of political and economic and necessarily moral governance that functions reasonably well, whose actors police and correct themselves when, inevitably, things go askew. I don’t think a reasonable observer can claim this describes the institutions of the United States right now. Laws are made of words. There is no rule of law in a society where Presidents argue over what “is” is, or claim “domestic” e-mails aren’t “targeted” to avoid discussing whether or not they are read. There is no rule of law when our leaders offer no language that meshes with commonsense reality, only phrases carefully parsed not to be caught out as outright lies while revealing as little truth as possible. There is no rule of law when members of incumbent power centers, in government or banking or the military, are almost never held to account for crimes that in ordinary life would be grave, while those they dislike are jailed naked and sleepless for the sin of betraying their secrets without any hint or allegation of malice.
Even in a good community, there is a role for secrets. I have taken some heat for defending, in principle, a role for opacity in banking, and would certainly defend a sphere of secrecy in diplomacy and governance. And it is always true that some cockroaches will thrive in the shadows. But though we may sometimes choose to blind ourselves, we ought not do so blindly. I might entrust my funds to a banker in promise of a sure return, but only if I have reason to believe, in the context of the web of institutions to which she belongs, she can be trusted to do reasonable things rather than steal the advance. I needn’t mislead myself that she is infallible. But I should know that in the unlikely event of a failure, it will be a virtuous failure, which in practice implies an accountable failure. Secrecy may be necessary, but it is intolerable without accountability, accountability in fact not in form. Our core institutions and the humans within them no longer hold themselves accountable for their large crimes, though they occasionally offer scapegoats from their ranks for small ones. They have evolved ingenious contrivances with elaborate rituals of accountability whose lack of substance is most invisible to the people enmeshed in them. This will kill us, is killing us, slowly and by degrees and not before it kills many other people. It is because I identify with my political community, because I do not exist except as a part of that community, that I am desperate to change this. I cannot be a good person, and I cannot be happy, when this is my polity.
The comfortable, “legitimate”, forms of accountability are failing, have failed. Whistleblowing is accountability by other means, and we need that, and ought to celebrate it. Our problem is not that it is done too frequently or too lightly. I might prefer Edward Snowden hadn’t gone to China(ish), but the health and virtue of my community is not a contest, not a rivalry with that or any other country. Contra Marshall, Snowden has “upended” nothing. Nothing he did prevents us from doing as much or as little surveillance as we, collectively, choose to do, and we may yet choose to do quite a lot of it. What Snowden has done is force us to own up, to stop pretending we are not doing what we all know we are doing, to stop pretending we do not know what is being done to us. It is on us, as a political community, to decide what we want to do and most importantly, how, on what terms, we want to do it. The people to whom we should listen the least are Dianne Feinstein and Barack Obama, John Boehner and Lindsay Graham, James Clapper. The tragedy is they probably have as hard time telling when they are lying as we do, they are so lost in it all. This isn’t their decision. This is our country.
It’s Not About Your Cat Photos
The government almost always abuses its surveillance powers. That should trouble every American citizen.
Since last week’s revelations about the NSA, skeptics have questioned whether expansive intelligence powers might really lead to civil liberties abuses. From a historical perspective, there’s no need to ask: Such abuses have occurred many, many times.
- by Beverly Gage
- June 10, 2013
Over the past century, American intelligence agencies have performed some amazing feats, outing Soviet infiltrators, hunting down terrorists, and keeping the homeland reasonably safe from its enemies. They have also used their powers to spy on millions of people engaged in legitimate political activity, and to go after critics in Congress, the media, and the public at large. Given this track record, it’s worth asking not whether such abuses might again occur, but whether we have sufficient reason to believe that they are notgoing to happen this time around.
To say that the expansion of surveillance powers comes with a high—and historically well-documented—risk of abuse is not to say that the NSA is interested in your cat photos. If you’ve never expressed an edgy political idea, you’re probably not at great personal risk. The people swept into the net at moments of expanded intelligence powers have almost always been outspoken political dissenters or critics of the intelligence establishment. The basic premise of the civil libertarian stance is that what happens to those people matters to all of us—not only because “we might be next” but because the free exchange of political ideas and criticism is the heart of American democracy.
So that’s the principle: Democracy requires protecting unpopular speech, and state surveillance tends to make people quiet. Then there’s the more practical side of things. In the past, when intelligence agencies have gained broad, unfettered powers, they have often used those powers not to protect the country but to protect themselves.
J. Edgar Hoover’s FBI stands as the example par excellence—an extreme but not fundamentally exceptional case of intelligence gathering gone awry. Last week I wrote a bit about COINTELPRO, the FBI’s notorious program of surveillance and disruption against targets ranging from Students for a Democratic Society to the Ku Klux Klan. But there’s another side to the FBI’s history of abuses—one that has less to do with attacks on political “subversives” than with the agency’s response to its mainstream critics.
Under Hoover the FBI devoted enormous resources to investigating people who publicly criticized intelligence operations or sought to challenge the powers of the FBI. Hoover’s targets extended from high-ranking members of the media and Congress down to ordinary citizens shooting the breeze. On one occasion, for instance, agents showed up to interview a Brooklyn liquor importer who had made the mistake of repeating a rumor that the FBI director might be “queer.” After a few minutes with the agents, who reminded him that Hoover’s “personal conduct is beyond reproach,” the man assured them that he held “no malice toward Mr. Hoover; that as a matter of fact he thinks Mr. Hoover has done a wonderful job.”
The interview had nothing to do with national security or even political dissent. But FBI agents didn’t necessarily view it that way. Charged with protecting American democracy from existential threats, they often saw themselves as a noble vanguard, possessed of secret, high-stakes knowledge, performing dangerous tasks that nobody else would or could. In this context, protecting the country meant protecting the FBI’s institutional power, and that meant protecting Hoover. If agents had qualms about this, there was little room to express them. To seriously criticize FBI policy, an employee would have had to do what NSA whistleblower Edward Snowden just did: give up a prosperous, interesting career and risk the wrath of a huge intelligence apparatus.
Even outside of the bureau, Hoover exercised powerful forms of control over potential critics. If the FBI learned a particularly juicy tidbit about a congressman, for instance, agents might show up at his office to let him know that his secrets—scandalous as they might be—were safe with the bureau. This had the predictable effect: Throughout the postwar years, Washington swirled with rumors that the FBI had a detailed file on every federal politician. There was some truth to the accusation. The FBI compiled background information on members of Congress, with an eye to both past scandals and to political ideology. But the files were probably not as extensive or all-encompassing as people believed them to be. The point was that it didn’t matter: The belief alone was enough to keep most politicians in line, and to keep them voting yes on FBI appropriations.
The same held true for members of the media. A critical column inevitably earned its author an FBI file. It might also come with a variety of other consequences. In 1936, when the famed columnist Westbrook Pegler mocked the FBI as a group of show-boaters, Hoover immediately removed him from the bureau’s media contact list, complaining that Pegler suffered from “mental halitosis.” Though Hoover and Pegler later reconciled, the FBI maintained a file on him for decades, just at it did for dozens of other media figures. Under this system, damning information could be leaked to more hospitable reporters (conservative columnist George Sokolsky was a particular favorite) or held for use at some future date.
One would hope that today’s NSA has better things to do than investigate its critics in the media, and that the safeguards now in place—congressional oversight committees, FISA courts—have in fact curtailed the kinds of abuses committed at Hoover’s FBI. But make no mistake: Those abuses occurred, and under the right circumstances they can occur again.
It’s Time to Rewrite the Internet to Give Us Better Privacy, and Security
It’s not too late to restore confidence, writes “digital Cassandra” Lawrence Lessig, but we need to start by asking the right questions.
by Lawrence Lessig Jun 12, 2013 4:45 AM EDT
Almost 15 years ago, as I was just finishing a book about the relationship between the Net (we called it “cyberspace” then) and civil liberties, a few ideas seemed so obvious as to be banal: First, life would move to the Net. Second, the Net would change as it did so. Gone would be simple privacy, the relatively anonymous default infrastructure for unmonitored communication; in its place would be a perpetually monitored, perfectly traceable system supporting both commerce and the government. That, at least, was the future that then seemed most likely, as business raced to make commerce possible and government scrambled to protect us (or our kids) from pornographers, and then pirates, and now terrorists.
But another future was also possible, and this was my third, and only important point: Recognizing these obvious trends, we just might get smart about how code (my shorthand for the technology of the Internet) regulates us, and just possibly might begin thinking smartly about how we could embed in that code the protections that the Constitution guarantees us. Because—and here was the punchline, the single slogan that all 724 people who read that book remember—code is law. And if code is law, then we need to be as smart about how code regulates us as we are about how the law does so.
There is, after all, something hopeful about a future that was smart about encoding our civil liberties. It could, in theory at least, be better. Better at protecting us from future Nixons, better at securing privacy, and better at identifying those keen to commit crime.
Think about this practically. Cyberanarchists notwithstanding, it was clear even in 1999 that there would be government and surveillance in cyberspace just as in real space. But the potential was that it could be better. Not just better only in finding the crook, but in not invading privacy. An FBI agent listening to a telephone call is always tempted to wander or misuse. S/he is human, and bad is in our blood. A computer sniffing for signals of crime only wanders as far as the code allows. And so the key is how and whether we regulate how far the code can wander—and do so both in law and in code.
None of this, it turned out, was obvious in 1999. I was deemed “a digital Cassandra” by David Pogue writing in The New York Times. “If you don’t like the Internet’s system, you can always flip off the modem,” he concluded. Sure. Turn off the machine, move to Iceland, and you’ll be just fine.
But what astonishes me is that today, more than a decade into the 21st century, the world has remained mostly oblivious to these obvious points about the relationship between law and code.
That’s the bit in the Edward Snowden interview that is, to me, the most shocking. As he explained to Glenn Greenwald:
The NSA specially targets the communications of everyone. It ingests them by default. It collects them in its system, and it filters them and it analyzes them and it measures them and it stores them for periods of time simply because that’s the easiest and the most efficient and most valuable way to achieve these ends ... Not all analysts have the ability to target everything. But I sitting at my desk certainly had the authority to wiretap anyone—from you [the reporter, Glenn Greenwald], to your accountant, to a federal judge, to even the president if I had a personal email.
We don’t know yet whether Snowden is telling the truth. Lots of people have denied specifics, and though his interview is compelling, just now, we literally don’t know.
But what we do know are the questions that ought to be asked in response to his claims. And specifically, this: Is it really the case that the government has entrusted our privacy to the good judgment of private analysts? Are there really no code-based controls for assuring that specific surveillance is specifically justified? And what is the technology for assuring that rogues paid by our government can’t use data collected by our government for purposes that none within our government would openly and publicly defend?
“Trust us” does not compute.Because the fact is that there is technology that could be deployed that would give many the confidence that none of us now have. “Trust us” does not compute. But trust and verify, with high-quality encryption, could. And there are companies, such as Palantir, developing technologies that could give us, and more importantly, reviewing courts, a very high level of confidence that data collected or surveilled was not collected or used in an improper way. Think of it as a massive audit log, recording how and who used what data for what purpose. We could code the Net in a string of obvious ways to give us even better privacy, while also enabling better security.
But we don’t, or haven’t, obviously. Maybe because of stupidity. How many congressmen could even describe how encryption works? Maybe because of cupidity. Who within our system can resist large and lucrative contracts to private companies, especially when bundled with generous campaign funding packages? Or maybe because the “permanent war” that Obama told us we were not in has actually convinced all within government that old ideas are dead and we just need to “get over it”—ideas like privacy, and due process, and fundamental proportionality.
These ideas may be dead, for now. And they will stay dead, in the future. At least until we finally learn how liberty can live in the digital age. And here’s the hint: not through law alone, but through law that demands code that even the Electronic Frontier Foundation could trust.
Web’s Reach Binds N.S.A. and Silicon Valley Leaders
WASHINGTON — When Max Kelly, the chief security officer for Facebook, left the social media company in 2010, he did not go to Google, Twitter or a similar Silicon Valley concern. Instead the man who was responsible for protecting the personal information of Facebook’s more than one billion users from outside attacks went to work for another giant institution that manages and analyzes large pools of data: the National Security Agency.
- by JAMES RISEN and NICK WINGFIELD
- June 19, 2013
Mr. Kelly’s move to the spy agency, which has not previously been reported, underscores the increasingly deep connections between Silicon Valley and the agency and the degree to which they are now in the same business. Both hunt for ways to collect, analyze and exploit large pools of data about millions of Americans.
The only difference is that the N.S.A. does it for intelligence, and Silicon Valley does it to make money.
The disclosure of the spy agency’s program called Prism, which is said to collect the e-mails and other Web activity of foreigners using major Internet companies like Google, Yahoo and Facebook, has prompted the companies to deny that the agency has direct access to their computers, even as they acknowledge complying with secret N.S.A. court orders for specific data.
Yet technology experts and former intelligence officials say the convergence between Silicon Valley and the N.S.A. and the rise of data mining — both as an industry and as a crucial intelligence tool — have created a more complex reality.
Silicon Valley has what the spy agency wants: vast amounts of private data and the most sophisticated software available to analyze it. The agency in turn is one of Silicon Valley’s largest customers for what is known as data analytics, one of the valley’s fastest-growing markets. To get their hands on the latest software technology to manipulate and take advantage of large volumes of data, United States intelligence agencies invest in Silicon Valley start-ups, award classified contracts and recruit technology experts like Mr. Kelly.
“We are all in these Big Data business models,” said Ray Wang, a technology analyst and chief executive of Constellation Research, based in San Francisco. “There are a lot of connections now because the data scientists and the folks who are building these systems have a lot of common interests.”
Although Silicon Valley has sold equipment to the N.S.A. and other intelligence agencies for a generation, the interests of the two began to converge in new ways in the last few years as advances in computer storage technology drastically reduced the costs of storing enormous amounts of data — at the same time that the value of the data for use in consumer marketing began to rise. “These worlds overlap,” said Philipp S. Krüger, chief executive of Explorist, an Internet start-up in New York.
The sums the N.S.A. spends in Silicon Valley are classified, as is the agency’s total budget, which independent analysts say is $8 billion to $10 billion a year.
Despite the companies’ assertions that they cooperate with the agency only when legally compelled, current and former industry officials say the companies sometimes secretly put together teams of in-house experts to find ways to cooperate more completely with the N.S.A. and to make their customers’ information more accessible to the agency. The companies do so, the officials say, because they want to control the process themselves. They are also under subtle but powerful pressure from the N.S.A. to make access easier.
Skype, the Internet-based calling service, began its own secret program, Project Chess, to explore the legal and technical issues in making Skype calls readily available to intelligence agencies and law enforcement officials, according to people briefed on the program who asked not to be named to avoid trouble with the intelligence agencies.
Project Chess, which has never been previously disclosed, was small, limited to fewer than a dozen people inside Skype, and was developed as the company had sometimes contentious talks with the government over legal issues, said one of the people briefed on the project. The project began about five years ago, before most of the company was sold by its parent, eBay, to outside investors in 2009. Microsoft acquired Skype in an $8.5 billion deal that was completed in October 2011.
A Skype executive denied last year in a blog post that recent changes in the way Skype operated were made at the behest of Microsoft to make snooping easier for law enforcement. It appears, however, that Skype figured out how to cooperate with the intelligence community before Microsoft took over the company, according to documents leaked by Edward J. Snowden, a former contractor for the N.S.A. One of the documents about the Prism program made public by Mr. Snowden says Skype joined Prism on Feb. 6, 2011.
Microsoft executives are no longer willing to affirm statements, made by Skype several years ago, that Skype calls could not be wiretapped. Frank X. Shaw, a Microsoft spokesman, declined to comment.
In its recruiting in Silicon Valley, the N.S.A. sends some of its most senior officials to lure the best of the best. No less than Gen. Keith B. Alexander, the agency’s director and the chief of the Pentagon’s Cyber Command, showed up at one of the world’s largest hacker conferences in Las Vegas last summer, looking stiff in an uncharacteristic T-shirt and jeans, to give the keynote speech. His main purpose at Defcon, the conference, was to recruit hackers for his spy agency.
N.S.A. badges are often seen on the lapels of officials at other technology and information security conferences. “They’re very open about their interest in recruiting from the hacker community,” said Jennifer Granick, the director of civil liberties at Stanford Law School’s Center for Internet and Society.
But perhaps no one embodies the tightening relationship between the N.S.A. and the valley more than Kenneth A. Minihan.
A career Air Force intelligence officer, Mr. Minihan was the director of the N.S.A. during the Clinton administration until his retirement in the late 1990s, and then he ran the agency’s outside professional networking organization. Today he is managing director of Paladin Capital Group, a venture capital firm based in Washington that in part specializes in financing start-ups that offer high-tech solutions for the N.S.A. and other intelligence agencies. In effect, Mr. Minihan is an advanced scout for the N.S.A. as it tries to capitalize on the latest technology to analyze and exploit the vast amounts of data flowing around the world and inside the United States.
The members of Paladin’s strategic advisory board include Richard C. Schaeffer Jr., a former N.S.A. executive. While Paladin is a private firm, the American intelligence community has its own in-house venture capital company, In-Q-Tel, financed by the Central Intelligence Agency to invest in high-tech start-ups.
Many software technology firms involved in data analytics are open about their connections to intelligence agencies. Gary King, a co-founder and chief scientist at Crimson Hexagon, a start-up in Boston, said in an interview that he had given talks at C.I.A. headquarters in Langley, Va., about his company’s social media analytics tools.
The future holds the prospect of ever greater cooperation between Silicon Valley and the N.S.A. because data storage is expected to increase at an annual compound rate of 53 percent through 2016, according to the International Data Corporation.
“We reached a tipping point, where the value of having user data rose beyond the cost of storing it,” said Dan Auerbach, a technology analyst with the Electronic Frontier Foundation, an electronic privacy group in San Francisco. “Now we have an incentive to keep it forever.”
Social media sites in the meantime are growing as voluntary data mining operations on a scale that rivals or exceeds anything the government could attempt on its own. “You willingly hand over data to Facebook that you would never give voluntarily to the government,” said Bruce Schneier, a technologist and an author.
James Risen reported from Washington, and Nick Wingfield from Seattle. Kitty Bennett contributed reporting.
Revealed: the top secret rules that allow NSA to use US data without a warrant
Fisa court submissions show broad scope of procedures governing NSA's surveillance of Americans' communication• Document one: procedures used by NSA to target non-US persons • Document two: procedures used by NSA to minimise data collected from US persons
Top secret documents submitted to the court that oversees surveillance by US intelligence agencies show the judges have signed off on broad orders which allow the NSA to make use of information "inadvertently" collected from domestic US communications without a warrant.
- by Glenn Greenwald, James Ball, Glenn Greenwald and James Ball
- June 20, 2013
The Guardian is publishing in full two documents submitted to the secret Foreign Intelligence Surveillance Court (known as the Fisa court), signed by Attorney General Eric Holder and stamped 29 July 2009. They detail the procedures the NSA is required to follow to target "non-US persons" under its foreign intelligence powers and what the agency does to minimize data collected on US citizens and residents in the course of that surveillance.
The documents show that even under authorities governing the collection of foreign intelligence from foreign targets, US communications can still be collected, retained and used.
The procedures cover only part of the NSA's surveillance of domestic US communications. The bulk collection of domestic call records, as first revealed by the Guardian earlier this month, takes place under rolling court orders issued on the basis of a legal interpretation of a different authority, section 215 of the Patriot Act.
The Fisa court's oversight role has been referenced many times by Barack Obama and senior intelligence officials as they have sought to reassure the public about surveillance, but the procedures approved by the court have never before been publicly disclosed.
The top secret documents published today detail the circumstances in which data collected on US persons under the foreign intelligence authority must be destroyed, extensive steps analysts must take to try to check targets are outside the US, and reveals how US call records are used to help remove US citizens and residents from data collection.
However, alongside those provisions, the Fisa court-approved policies allow the NSA to:
• Keep data that could potentially contain details of US persons for up to five years;
• Retain and make use of "inadvertently acquired" domestic communications if they contain usable intelligence, information on criminal activity, threat of harm to people or property, are encrypted, or are believed to contain any information relevant to cybersecurity;
• Preserve "foreign intelligence information" contained within attorney-client communications;
• Access the content of communications gathered from "U.S. based machine"or phone numbers in order to establish if targets are located in the US, for the purposes of ceasing further surveillance.
The broad scope of the court orders, and the nature of the procedures set out in the documents, appear to clash with assurances from President Obama and senior intelligence officials that the NSA could not access Americans' call or email information without warrants.
The documents also show that discretion as to who is actually targeted under the NSA's foreign surveillance powers lies directly with its own analysts, without recourse to courts or superiors – though a percentage of targeting decisions are reviewed by internal audit teams on a regular basis.
Since the Guardian first revealed the extent of the NSA's collection of US communications, there have been repeated calls for the legal basis of the programs to be released. On Thursday, two US congressmen introduced a bill compelling the Obama administration to declassify the secret legal justifications for NSA surveillance.
The disclosure bill, sponsored by Adam Schiff, a California Democrat, and Todd Rokita, an Indiana Republican, is a complement to one proposed in the Senate last week. It would "increase the transparency of the Fisa Court and the state of the law in this area," Schiff told the Guardian. "It would give the public a better understanding of the safeguards, as well as the scope of these programs."
Section 702 of the Fisa Amendments Act (FAA), which was renewed for five years last December, is the authority under which the NSA is allowed to collect large-scale data, including foreign communications and also communications between the US and other countries, provided the target is overseas.
FAA warrants are issued by the Fisa court for up to 12 months at a time, and authorise the collection of bulk information – some of which can include communications of US citizens, or people inside the US. To intentionally target either of those groups requires an individual warrant.
One-paragraph order
One such warrant seen by the Guardian shows that they do not contain detailed legal rulings or explanation. Instead, the one-paragraph order, signed by a Fisa court judge in 2010, declares that the procedures submitted by the attorney general on behalf of the NSA are consistent with US law and the fourth amendment.
Those procedures state that the "NSA determines whether a person is a non-United States person reasonably believed to be outside the United States in light of the totality of the circumstances based on the information available with respect to that person, including information concerning the communications facility or facilities used by that person".
It includes information that the NSA analyst uses to make this determination - including IP addresses, statements made by the potential target, and other information in the NSA databases, which can include public information and data collected by other agencies.
Where the NSA has no specific information on a person's location, analysts are free to presume they are overseas, the document continues.
"In the absence of specific information regarding whether a target is a United States person," it states "a person reasonably believed to be located outside the United States or whose location is not known will be presumed to be a non-United States person unless such person can be positively identified as a United States person."
If it later appears that a target is in fact located in the US, analysts are permitted to look at the content of messages, or listen to phone calls, to establish if this is indeed the case.
Referring to steps taken to prevent intentional collection of telephone content of those inside the US, the document states: "NSA analysts may analyze content for indications that a foreign target has entered or intends to enter the United States. Such content analysis will be conducted according to analytic and intelligence requirements and priorities."
Details set out in the "minimization procedures", regularly referred to in House and Senate hearings, as well as public statements in recent weeks, also raise questions as to the extent of monitoring of US citizens and residents.
NSA minimization procedures signed by Holder in 2009 sets out that once a target is confirmed to be within the US, interception must stop immediately. However, these circumstances do not apply to large-scale data where the NSA claims it is unable to filter US communications from non-US ones.
The NSA is empowered to retain data for up to five years and the policy states "communications which may be retained include electronic communications acquired because of limitations on the NSA's ability to filter communications".
Even if upon examination a communication is found to be domestic – entirely within the US – the NSA can appeal to its director to keep what it has found if it contains "significant foreign intelligence information", "evidence of a crime", "technical data base information" (such as encrypted communications), or "information pertaining to a threat of serious harm to life or property".
Domestic communications containing none of the above must be destroyed. Communications in which one party was outside the US, but the other is a US-person, are permitted for retention under FAA rules.
The minimization procedure adds that these can be disseminated to other agencies or friendly governments if the US person is anonymised, or including the US person's identity under certain criteria.
A separate section of the same document notes that as soon as any intercepted communications are determined to have been between someone under US criminal indictment and their attorney, surveillance must stop. However, the material collected can be retained, if it is useful, though in a segregated database:
"The relevant portion of the communication containing that conversation will be segregated and the National Security Division of the Department of Justice will be notified so that appropriate procedures may be established to protect such communications from review or use in any criminal prosecution, while preserving foreign intelligence information contained therein," the document states.
In practice, much of the decision-making appears to lie with NSA analysts, rather than the Fisa court or senior officials.
A transcript of a 2008 briefing on FAA from the NSA's general counsel sets out how much discretion NSA analysts possess when it comes to the specifics of targeting, and making decisions on who they believe is a non-US person. Referring to a situation where there has been a suggestion a target is within the US.
"Once again, the standard here is a reasonable belief that your target is outside the United States. What does that mean when you get information that might lead you to believe the contrary? It means you can't ignore it. You can't turn a blind eye to somebody saying: 'Hey, I think so and so is in the United States.' You can't ignore that. Does it mean you have to completely turn off collection the minute you hear that? No, it means you have to do some sort of investigation: 'Is that guy right? Is my target here?" he says.
"But, if everything else you have says 'no' (he talked yesterday, I saw him on TV yesterday, even, depending on the target, he was in Baghdad) you can still continue targeting but you have to keep that in mind. You can't put it aside. You have to investigate it and, once again, with that new information in mind, what is your reasonable belief about your target's location?"
The broad nature of the court's oversight role, and the discretion given to NSA analysts, sheds light on responses from the administration and internet companies to the Guardian's disclosure of the PRISM program. They have stated that the content of online communications is turned over to the NSA only pursuant to a court order. But except when a US citizen is specifically targeted, the court orders used by the NSA to obtain that information as part of Prism are these general FAA orders, not individualized warrants specific to any individual.
Once armed with these general orders, the NSA is empowered to compel telephone and internet companies to turn over to it the communications of any individual identified by the NSA. The Fisa court plays no role in the selection of those individuals, nor does it monitor who is selected by the NSA
The NSA's ability to collect and retain the communications of people in the US, even without a warrant, has fuelled congressional demands for an estimate of how many Americans have been caught up in surveillance.
Two US senators, Ron Wyden and Mark Udall – both members of the Senate intelligence committee – have been seeking this information since 2011, but senior White House and intelligence officials have repeatedly insisted that the agency is unable to gather such statistics.
http://www.guardian.co.uk/world/interactive/2013/jun/20/exhibit-a-procedures-nsa-documentProcedures used by NSA to target non-US persons: Exhibit A – full document
Top-secret documents show Fisa judges have signed off on broad orders allowing the NSA to make use of information 'inadvertently' collected from domestic US communications without a warrant
http://www.guardian.co.uk/world/interactive/2013/jun/20/exhibit-b-nsa-procedures-documentProcedures used by NSA to minimize data collection from US persons: Exhibit B – full document
The documents detail the procedures the NSA is required to follow to target 'non-US persons' under its foreign intelligence powers – and what the agency does to minimize data collected on US citizens and residents
The Intelligence Community’s Willful Ignorance about Americans Caught in 702 Surveillance
Given the Intelligence Community’s reluctant and partial disclosures on the Section 702 (PRISM/FAA) collection, I want to return to a squabble from last fall, before Congress reauthorized FAA.
- by emptywheel
- June 20, 2013
- Read Later
As you’ll recall, Ron Wyden tried to get the IC to disclose the number of Americans whose communication had been reviewed under Section 702. The IC dicked around long enough to ensure Wyden didn’t get an answer in time to make a political stink about it. When they finally gave him an answer, they said providing such a number would violate the privacy of Americans.
I defer to [the NSA Inspector General's] conclusion that obtaining such an estimate was beyond the capacity of his office and dedicating sufficient additional resources would likely impede the NSA’s mission. He further stated that his office and NSA leadership agreed that an IG review of the sort suggested would itself violate the privacy of U.S. persons.Ultimately, this statement seemed to be as much about resource allocation as anything else — the NSA and IC IGs would need more staff to accomplish the tast. (I must say, I do find it interesting the ICIG has time to investigate 375 leaks but not enough time to find out how many Americans are being spied on.)
But look at how closely the government is purportedly tracking US person data.
These procedures require that the acquisition of information is conducted, to the greatest extent reasonably feasible, to minimize the acquisition of information not relevant to the authorized foreign intelligence purpose.Now, these passages ought to make people more worried about privacy than not. Stated clearly, it says the government believes it can collect and keep US person content if it deems that content “relevant” to the reason they collected the information.
Any inadvertently acquired communication of or concerning a U.S. person must be promptly destroyed if it is neither relevant to the authorized purpose nor evidence of a crime.
[snip]
Any information collected after a foreign target enters the U.S. –or prior to a discovery that any target erroneously believed to be foreign was in fact a U.S. person– must be promptly destroyed unless that information meets specific, limited criteria approved by the Foreign Intelligence Surveillance Court.
The dissemination of any information about U.S. persons is expressly prohibited unless it is necessary to understand foreign intelligence or assess its importance; is evidence of a crime; or indicates a threat of death or serious bodily harm.
Remember two things: this collection is not limited to use with terrorism; it can be used for espionage investigations, hacking, or any foreign intelligence purpose. And the government has already deemed every single one of our phone records to be “relevant” to an umbrella terror investigation, so the definition of relevance the government has developed in secret is unbelievably broad and persmissive.
That collection — the people whose content is reviewed and deemed relevant and kept — is the universe of people Wyden wanted to count. And the government is making decisions about the relevance of them in secret, but not tracking the process by which they do so.
Note too that the government can disseminate US person communications if “it is necessary to understand foreign intelligence.” This is not news (which is why it is so appalling that people were fighting over whether the government could listen to US person calls or read their emails). It is part of traditional FISA, too. (It was using that excuse that John Bolton was learning about what his rivals were negotiating with the North Koreans.) But given how much more information an analyst can access both because she is accessing all Internet activity and not just phone, but also because more associated communications are sucked up with a target, it means many more US persons’ communications might be disseminated. It’s not clear, by the way, such dissemination would exclude privileged conversations between lawyers and clients, or discussions between journalists and sources.
And this second group of people — the ones whose communications are being circulated — are counted.
Though we’re not allowed to know what those numbers are.
Here’s what the DOJ Inspector General Michael Horowitz had to say about a statutorily required review of the 702 collection he recently completed (I think, but it’s not entirely clear, that Horowitz didn’t finish this review until after FAA was renewed last year — I know he didn’t finish it before the Judiciary and Intelligence Committees passed it out).
Inspector General Michael E. Horowitz of the United States Department of Justice Office of the Inspector General (OIG) recently issued a report examining the activities of the Federal Bureau of Investigation (FBI) under Section 702 of the Foreign Intelligence Surveillance Act Amendments Act of 2008 (Act). Section 702 authorizes the targeting of non-U.S. persons reasonably believed to be outside the United States for the purpose of acquiring foreign intelligence information. The Act required that the Inspector General conduct a review of the Department’s role in this process and, in conjunction with this review, the OIG reviewed the number of disseminated FBI intelligence reports containing a reference to a U.S. person identity, the number of U.S. person identities subsequently disseminated in response to requests for identities not referred to by name or title in the original reporting, the number of targets later determined to be located in the United States, and whether communications of such targets were reviewed. See 50 U.S.C. 1881a(l)(2)(B) and (C). The OIG also reviewed the FBI’s compliance with the targeting and minimization procedures required under the Act.In other words, the DOJ IG counted — because the law required him to — the following:
The final report has been issued and delivered to the relevant Congressional oversight and intelligence committees, as well as leadership offices. Because the report is classified, its contents cannot be disclosed to the public.
But it did not count how many US persons’ communications were reviewed but not disseminated, many of which may be retained under the relevance standard.
- The number of US person-related communication that got disseminated in a first dissemination of intelligence
- The number of US persons whose identity identified in a follow-up on an original dissemination
- The number of targets originally believed to be foreign who end up being US persons (note, the NSA conveniently doesn’t explain what the specific criteria are that would allow the government to keep these communications … I wonder why?)
In general, when the government chooses not to count things, there’s a reason it doesn’t want to.
No One is Innocent
by Alex Tabarrok on June 21, 2013 at 7:22 am in History, Law, Political Science | Permalink
I broke the law yesterday and again today and I will probably break the law tomorrow. Don’t mistake me, I have done nothing wrong. I don’t even know what laws I have broken. Nevertheless, I am reasonably confident that I have broken some laws, rules, or regulations recently because its hard for anyone to live today without breaking the law. Doubt me? Have you ever thrown out some junk mail that came to your house but was addressed to someone else? That’s a violation of federal law punishable by up to 5 years in prison.
Harvey Silverglate argues that a typical American commits three felonies a day. I think that number is too high but it is easy to violate the law without intent or knowledge. Most crimes used to be based on the common law and ancient understandings of wrong (murder, assault, theft and so on) but today there are thousands of federal criminal laws that bear no relation to common law or common understanding. The WSJ illustrates:
Last September (2011), retired race-car champion Bobby Unser told a congressional hearing about his 1996 misdemeanor conviction for accidentally driving a snowmobile onto protected federal land, violating the Wilderness Act, while lost in a snowstorm. Though the judge gave him only a $75 fine, the 77-year-old racing legend got a criminal record.Or how about this:
Mr. Unser says he was charged after he went to authorities for help finding his abandoned snowmobile. “The criminal doesn’t usually call the police for help,” he says.
In 2009, Mr. Anderson loaned his son some tools to dig for arrowheads near a favorite campground of theirs. Unfortunately, they were on federal land….The Anderson’s didn’t even find any arrowheads but the attempt to find was punishable by imprisonment. Under statutes such as the Lacey Act one can even face criminal prosecution for violating the laws of another country. Ignorance of another country’s laws is no excuse.
There is no evidence the Andersons intended to break the law, or even knew the law existed, according to court records and interviews. But the law, the Archaeological Resources Protection Act of 1979, doesn’t require criminal intent and makes it a felony punishable by up to two years in prison to attempt to take artifacts off federal land without a permit.
If someone tracked you for a year are you confident that they would find no evidence of a crime? Remember, under the common law, mens rea, criminal intent, was a standard requirement for criminal prosecution but today that is typically no longer the case especially under federal criminal law .
Faced with the evidence of an non-intentional crime, most prosecutors, of course, would use their discretion and not threaten imprisonment. Evidence and discretion, however, are precisely the point. Today, no one is innocent and thus our freedom is maintained only by the high cost of evidence and the prosecutor’s discretion.
One of the responses to the revelations about the mass spying on Americans by the NSA and other agencies is “I have nothing to hide. What me worry?” I tweeted in response “If you have nothing to hide, you live a boring life.” More fundamentally, the NSA spying machine has reduced the cost of evidence so that today our freedom–or our independence–is to a large extent at the discretion of those in control of the panopticon.
The Surveillance-Marketing Complex, Coming Soon to a Computer Near You
—By Kevin Drum
| Fri Jun. 21, 2013 3:00 AM PDT
Here's a quote that should probably scare you:
"We are all in these Big Data business models."Why scary? Because the "we" in this case is Silicon Valley and the American intelligence community. As James Risen and Nick Wingfield reported yesterday in the New York Times, the interests of tech companies and the NSA have been coverging over the past decade in two ways. The first way is fairly prosaic: lots of Silicon Valley companies are in the business of selling stuff to the NSA: storage hardware, sophisticated communications equipment, data analytics software, and more. But while this may have increased recently, it's not fundamentally new. It's just the latest high-tech twist on the good old military-industrial complex.
But there's a second way that the interests of Fort Meade and Santa Clara County have converged: these days, they're fundamentally in the same business. The NSA calls it surveillance, and all the rest of us just call it spying. Silicon Valley, conversely, wouldn't be caught dead calling it that. They call it "targeted advertising" or "monetizing the social network." But it's pretty much the same thing.
When your local grocery chain gives you a loyalty card, do you think they're doing it in order to make you a loyal customer? Of course not. After all, every other supermarket offers loyalty cards too. So why are they willing to offer such eye-watering discounts if you use one? Because it allows them to track every single purchase you make and dump the information into a gigantic database. That's useful to them, and, more importantly, it's valuable data to sell to others. That's why they want it so badly.
Online, of course, similar things are happening. High-tech marketing firms are busily figuring out ways to merge data from lots of different sources to build a profile of you that would probably put your own mother to shame. Why? Because it's worth a lot of money. Advertisers are willing to pay huge amounts of money to be able to target the 1 percent of prospects who are actually likely to buy their wares, instead of simply blasting their message out to everyone. Target, for example, figured out the shopping habits of pregnant women and used that to create highly effective marketing campaigns aimed at expectant mothers. That's a lucrative market.
Combine that with Facebook likes, Google searches, phone records, pharmacy records, and every other digital trail that all of us leave behind us, and what can't you predict? We don't know yet, but there are sure plenty of people beavering away to find out.
Needless to say, spy agencies have exactly the same goals. They might not be interested in whether you're pregnant—though, then again, they might be—but they're keenly interested in trying to predict future actions based on past events. So when Risen and Wingfield report that Facebook's chief security officer decamped for a job with the NSA a couple of years ago, should we be surprised? Not a bit. They're both in the same business, after all.
We can all decide for ourselves whether we think the NSA should have access to all our phone records. But the surveillance state doesn't end there. Keep in mind that DARPA's first crack at this stuff in the wake of 9/11 was called Total Information Awareness, and its goal was precisely what the name implied: a wide-ranging database that included personal e-mails, social networks, credit card records, phone calls, medical records, shopping records, travel data, and anything else that the marriage of high tech and modern marketing made possible. TIA got killed after public outcry, but it never really went away. How could it? The merger of public and private spying is just too powerful to ignore.
So even if you're not too worried about NSA's collection of phone records, you'd do well to think about where this is likely to go. There will be other terrorist attacks, and in their aftermath the public will be less likely to object to things like TIA than they were the first time around. After all, we're all used to Facebook spying on us these days. (There's no need to mince words about what they do, is there?) So as scary as a surveillance state may be, it's not the worst thing that could happen. That's because the private sector spies on us too, and they do it so charmingly that not only don't we object, we practically beg them to do more. Instead of a military-industrial complex, we're rapidly moving toward a marriage so perfect that eHarmony could only dream of it: the surveillance-marketing complex.
Pretty sure I posted a clearer and more concise version of this three days ago.
GCHQ taps fibre-optic cables for secret access to world's communications
Exclusive: British spy agency collects and stores vast quantities of global email messages, Facebook posts, internet histories and calls, and shares them with NSA, latest documents from Edward Snowden reveal
- by Ewen MacAskill, Julian Borger, Nick Hopkins, Nick Davies, James Ball, Ewen MacAskill, Julian Borger, Nick Hopkins, Nick Davies and James Ball
- June 21, 2013
- Read Later
Secret document detailing GCHQ's ambition to 'master the internet'
Britain's spy agency GCHQ has secretly gained access to the network of cables which carry the world's phone calls and internet traffic and has started to process vast streams of sensitive personal information which it is sharing with its American partner, the National Security Agency (NSA).
The sheer scale of the agency's ambition is reflected in the titles of its two principal components: Mastering the Internet and Global Telecoms Exploitation, aimed at scooping up as much online and telephone traffic as possible. This is all being carried out without any form of public acknowledgement or debate.
One key innovation has been GCHQ's ability to tap into and store huge volumes of data drawn from fibre-optic cables for up to 30 days so that it can be sifted and analysed. That operation, codenamed Tempora, has been running for some 18 months.
GCHQ and the NSA are consequently able to access and process vast quantities of communications between entirely innocent people, as well as targeted suspects.
This includes recordings of phone calls, the content of email messages, entries on Facebook and the history of any internet user's access to websites – all of which is deemed legal, even though the warrant system was supposed to limit interception to a specified range of targets.
The existence of the programme has been disclosed in documents shown to the Guardian by the NSA whistleblower Edward Snowden as part of his attempt to expose what he has called "the largest programme of suspicionless surveillance in human history".
"It's not just a US problem. The UK has a huge dog in this fight," Snowden told the Guardian. "They [GCHQ] are worse than the US."
However, on Friday a source with knowledge of intelligence argued that the data was collected legally under a system of safeguards, and had provided material that had led to significant breakthroughs in detecting and preventing serious crime.
Britain's technical capacity to tap into the cables that carry the world's communications – referred to in the documents as special source exploitation – has made GCHQ an intelligence superpower.
By 2010, two years after the project was first trialled, it was able to boast it had the "biggest internet access" of any member of the Five Eyes electronic eavesdropping alliance, comprising the US, UK, Canada, Australia and New Zealand.
UK officials could also claim GCHQ "produces larger amounts of metadata than NSA". (Metadata describes basic information on who has been contacting whom, without detailing the content.)
By May last year 300 analysts from GCHQ, and 250 from the NSA, had been assigned to sift through the flood of data.
The Americans were given guidelines for its use, but were told in legal briefings by GCHQ lawyers: "We have a light oversight regime compared with the US".
When it came to judging the necessity and proportionality of what they were allowed to look for, would-be American users were told it was "your call".
The Guardian understands that a total of 850,000 NSA employees and US private contractors with top secret clearance had access to GCHQ databases.
The documents reveal that by last year GCHQ was handling 600m "telephone events" each day, had tapped more than 200 fibre-optic cables and was able to process data from at least 46 of them at a time.
Document quoting Lt Gen Keith Alexander, head of the NSA, during a visit to Britain
Each of the cables carries data at a rate of 10 gigabits per second, so the tapped cables had the capacity, in theory, to deliver more than 21 petabytes a day – equivalent to sending all the information in all the books in the British Library 192 times every 24 hours.
And the scale of the programme is constantly increasing as more cables are tapped and GCHQ data storage facilities in the UK and abroad are expanded with the aim of processing terabits (thousands of gigabits) of data at a time.
For the 2 billion users of the world wide web, Tempora represents a window on to their everyday lives, sucking up every form of communication from the fibre-optic cables that ring the world.
The NSA has meanwhile opened a second window, in the form of the Prism operation, revealed earlier this month by the Guardian, from which it secured access to the internal systems of global companies that service the internet.
The GCHQ mass tapping operation has been built up over five years by attaching intercept probes to transatlantic fibre-optic cables where they land on British shores carrying data to western Europe from telephone exchanges and internet servers in north America.
This was done under secret agreements with commercial companies, described in one document as "intercept partners".
The papers seen by the Guardian suggest some companies have been paid for the cost of their co-operation and GCHQ went to great lengths to keep their names secret. They were assigned "sensitive relationship teams" and staff were urged in one internal guidance paper to disguise the origin of "special source" material in their reports for fear that the role of the companies as intercept partners would cause "high-level political fallout".
The source with knowledge of intelligence said on Friday the companies were obliged to co-operate in this operation. They are forbidden from revealing the existence of warrants compelling them to allow GCHQ access to the cables.
"There's an overarching condition of the licensing of the companies that they have to co-operate in this. Should they decline, we can compel them to do so. They have no choice."
The source said that although GCHQ was collecting a "vast haystack of data" what they were looking for was "needles".
"Essentially, we have a process that allows us to select a small number of needles in a haystack. We are not looking at every piece of straw. There are certain triggers that allow you to discard or not examine a lot of data so you are just looking at needles. If you had the impression we are reading millions of emails, we are not. There is no intention in this whole programme to use it for looking at UK domestic traffic – British people talking to each other," the source said.
He explained that when such "needles" were found a log was made and the interception commissioner could see that log.
"The criteria are security, terror, organised crime. And economic well-being. There's an auditing process to go back through the logs and see if it was justified or not. The vast majority of the data is discarded without being looked at … we simply don't have the resources."
However, the legitimacy of the operation is in doubt. According to GCHQ's legal advice, it was given the go-ahead by applying old law to new technology. The 2000 Regulation of Investigatory Powers Act (Ripa) requires the tapping of defined targets to be authorised by a warrant signed by the home secretary or foreign secretary.
However, an obscure clause allows the foreign secretary to sign a certificate for the interception of broad categories of material, as long as one end of the monitored communications is abroad. But the nature of modern fibre-optic communications means that a proportion of internal UK traffic is relayed abroad and then returns through the cables.
Parliament passed the Ripa law to allow GCHQ to trawl for information, but it did so 13 years ago with no inkling of the scale on which GCHQ would attempt to exploit the certificates, enabling it to gather and process data regardless of whether it belongs to identified targets.
The categories of material have included fraud, drug trafficking and terrorism, but the criteria at any one time are secret and are not subject to any public debate. GCHQ's compliance with the certificates is audited by the agency itself, but the results of those audits are also secret.
An indication of how broad the dragnet can be was laid bare in advice from GCHQ's lawyers, who said it would be impossible to list the total number of people targeted because "this would be an infinite list which we couldn't manage".
There is an investigatory powers tribunal to look into complaints that the data gathered by GCHQ has been improperly used, but the agency reassured NSA analysts in the early days of the programme, in 2009: "So far they have always found in our favour".
Historically, the spy agencies have intercepted international communications by focusing on microwave towers and satellites. The NSA's intercept station at Menwith Hill in North Yorkshire played a leading role in this. One internal document quotes the head of the NSA, Lieutenant General Keith Alexander, on a visit to Menwith Hill in June 2008, asking: "Why can't we collect all the signals all the time? Sounds like a good summer project for Menwith."
By then, however, satellite interception accounted for only a small part of the network traffic. Most of it now travels on fibre-optic cables, and the UK's position on the western edge of Europe gave it natural access to cables emerging from the Atlantic.
The data collected provides a powerful tool in the hands of the security agencies, enabling them to sift for evidence of serious crime. According to the source, it has allowed them to discover new techniques used by terrorists to avoid security checks and to identify terrorists planning atrocities. It has also been used against child exploitation networks and in the field of cyberdefence.
It was claimed on Friday that it directly led to the arrest and imprisonment of a cell in the Midlands who were planning co-ordinated attacks; to the arrest of five Luton-based individuals preparing acts of terror, and to the arrest of three London-based people planning attacks prior to the Olympics.
As the probes began to generate data, GCHQ set up a three-year trial at the GCHQ station in Bude, Cornwall. By the summer of 2011, GCHQ had probes attached to more than 200 internet links, each carrying data at 10 gigabits a second. "This is a massive amount of data!" as one internal slideshow put it. That summer, it brought NSA analysts into the Bude trials. In the autumn of 2011, it launched Tempora as a mainstream programme, shared with the Americans.
The intercept probes on the transatlantic cables gave GCHQ access to its special source exploitation. Tempora allowed the agency to set up internet buffers so it could not simply watch the data live but also store it – for three days in the case of content and 30 days for metadata.
"Internet buffers represent an exciting opportunity to get direct access to enormous amounts of GCHQ's special source data," one document explained.
The processing centres apply a series of sophisticated computer programmes in order to filter the material through what is known as MVR – massive volume reduction. The first filter immediately rejects high-volume, low-value traffic, such as peer-to-peer downloads, which reduces the volume by about 30%. Others pull out packets of information relating to "selectors" – search terms including subjects, phone numbers and email addresses of interest. Some 40,000 of these were chosen by GCHQ and 31,000 by the NSA. Most of the information extracted is "content", such as recordings of phone calls or the substance of email messages. The rest is metadata.
The GCHQ documents that the Guardian has seen illustrate a constant effort to build up storage capacity at the stations at Cheltenham, Bude and at one overseas location, as well a search for ways to maintain the agency's comparative advantage as the world's leading communications companies increasingly route their cables through Asia to cut costs. Meanwhile, technical work is ongoing to expand GCHQ's capacity to ingest data from new super cables carrying data at 100 gigabits a second. As one training slide told new users: "You are in an enviable position – have fun and make the most of it."
Yours you fucking dummy.
Do You Have ANY IDEA How Widespread Government Spying Really Is?
You’ve Heard that the Government and Big Corporations Are Spying. But Do You Have ANY IDEA How Widespread the Spying Really Is?
- by Washingtons Blog
- Read Later
Preface: Americans now know that the government is spying. But they still have no idea how many of their communications and activities are being surveilled … or what might be done with that information.
Yes, the Government Is Spying On You
You know that the government has been caught spying on the Verizon phone calls of tens of millions of Americans. The spying effort specifically targeted Americans living on U.S. soil.
And as NBC News reports:
NBC News has learned that under the post-9/11 Patriot Act, the government has been collecting records on every phone call made in the U.S.This includes metadata … which can tell the government a lot about you. And it also includes content.
In addition, a government expert told the Washington Post that the government “quite can literally watch your ideas form as you type.” A top NSA executives have confirmed to Washington’s Blog that the NSA is intercepting and storing virtually all digital communications on the Internet.
Private contractors can also view all of your data … and the government isn’t keeping track of which contractors see your data and which don’t.
And top NSA and FBI experts say that the government can retroactively search all of the collected information on someone since 9/11 if they suspect someone of wrongdoing … or want to frame him.
The American government is in fact collecting and storing virtually every phone call, purchases, email, text message, internet searches, social media communications, health information, employment history, travel and student records, and virtually all other information of every American.
The Wall Street Journal reported that the NSA spies on Americans’ credit card transactions as well.
In fact, all U.S. intelligence agencies – including the CIA and NSA – are going to spy on Americans’ finances. The IRS will be spying on Americans’ shopping records, travel, social interactions, health records and files from other government investigators.
The government is flying drones over the American homeland to spy on us. Indeed, the head of the FBI told Congress today that drones are used for domestic surveillance … and that there are no rules in place governing spying on Americans with drones.
Senator Rand Paul correctly notes:
The domestic use of drones to spy on Americans clearly violates the Fourth Amendment and limits our rights to personal privacy.Emptywheel notes in a post entitled “The OTHER Assault on the Fourth Amendment in the NDAA? Drones at Your Airport?”:
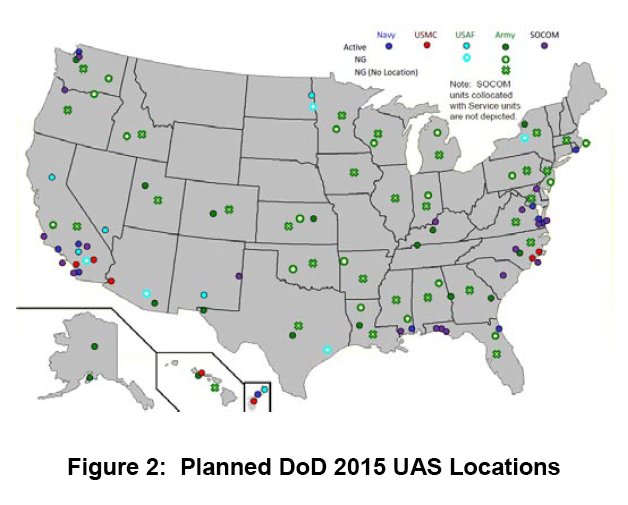
***Many police departments are also using drones to spy on us. As the Hill reported:
As the map above makes clear–taken from this 2010 report–DOD [the Department of Defense] plans to have drones all over the country by 2015.
At least 13 state and local police agencies around the country have used drones in the field or in training, according to the Association for Unmanned Vehicle Systems International, an industry trade group. The Federal Aviation Administration has predicted that by the end of the decade, 30,000 commercial and government drones could be flying over U.S. skies.Moreover, Wired reports:
***
“Drones should only be used if subject to a powerful framework that regulates their use in order to avoid abuse and invasions of privacy,” Chris Calabrese, a legislative counsel for the American Civil Liberties Union, said during a congressional forum in Texas last month.
He argued police should only fly drones over private property if they have a warrant, information collected with drones should be promptly destroyed when it’s no longer needed and domestic drones should not carry any weapons.
He argued that drones pose a more serious threat to privacy than helicopters because they are cheaper to use and can hover in the sky for longer periods of time.
A congressional report earlier this year predicted that drones could soon be equipped with technologies to identify faces or track people based on their height, age, gender and skin color.
Transit authorities in cities across the country are quietly installing microphone-enabled surveillance systems on public buses that would give them the ability to record and store private conversations….RT notes:
The systems are being installed in San Francisco, Baltimore, and other cities with funding from the Department of Homeland Security in some cases ….
The IP audio-video systems can be accessed remotely via a built-in web server (.pdf), and can be combined with GPS data to track the movement of buses and passengers throughout the city.
***
The systems use cables or WiFi to pair audio conversations with camera images in order to produce synchronous recordings. Audio and video can be monitored in real-time, but are also stored onboard in blackbox-like devices, generally for 30 days, for later retrieval. Four to six cameras with mics are generally installed throughout a bus, including one near the driver and one on the exterior of the bus.
***
Privacy and security expert Ashkan Soltani told the Daily that the audio could easily be coupled with facial recognition systems or audio recognition technology to identify passengers caught on the recordings.
Street lights that can spy installed in some American citiesCell towers track where your phone is at any moment, and the major cell carriers, including Verizon and AT&T, responded to at least 1.3 million law enforcement requests for cell phone locations and other data in 2011. (And – given that your smartphone routinely sends your location information back to Apple or Google – it would be child’s play for the government to track your location that way.) Your iPhone, or other brand of smartphone is spying on virtually everything you do (ProPublica notes: “That’s No Phone. That’s My Tracker“).
America welcomes a new brand of smart street lightning systems: energy-efficient, long-lasting, complete with LED screens to show ads. They can also spy on citizens in a way George Orwell would not have imagined in his worst nightmare.
With a price tag of $3,000+ apiece, according to an ABC report, the street lights are now being rolled out in Detroit, Chicago and Pittsburgh, and may soon mushroom all across the country.
Part of the Intellistreets systems made by the company Illuminating Concepts, they have a number of “homeland security applications” attached.
Each has a microprocessor “essentially similar to an iPhone,” capable of wireless communication. Each can capture images and count people for the police through a digital camera, record conversations of passers-by and even give voice commands thanks to a built-in speaker.
Ron Harwood, president and founder of Illuminating Concepts, says he eyed the creation of such a system after the 9/11 terrorist attacks and the Hurricane Katrina disaster. He is “working with Homeland Security” to deliver his dream of making people “more informed and safer.”
Fox news notes that the government is insisting that “black boxes” be installed in cars to track your location.
The TSA has moved way past airports, trains and sports stadiums, and is deploying mobile scanners to spy on people all over the place. This means that traveling within the United States is no longer a private affair.
You might also have seen the news this week that the Department of Homeland Security is going to continue to allow searches of laptops and phones based upon “hunches”.
What’s that about?
The ACLU published a map in 2006 showing that nearly two-thirds of the American public – 197.4 million people – live within a “constitution-free zone” within 100 miles of land and coastal borders:
The ACLU explained:
- Normally under the Fourth Amendment of the U.S. Constitution, the American people are not generally subject to random and arbitrary stops and searches.
- The border, however, has always been an exception. There, the longstanding view is that the normal rules do not apply. For example the authorities do not need a warrant or probable cause to conduct a “routine search.”
- But what is “the border”? According to the government, it is a 100-mile wide strip that wraps around the “external boundary” of the United States.
- As a result of this claimed authority, individuals who are far away from the border, American citizens traveling from one place in America to another, are being stopped and harassed in ways that our Constitution does not permit.
- Border Patrol has been setting up checkpoints inland — on highways in states such as California, Texas and Arizona, and at ferry terminals in Washington State. Typically, the agents ask drivers and passengers about their citizenship. Unfortunately, our courts so far have permitted these kinds of checkpoints – legally speaking, they are “administrative” stops that are permitted only for the specific purpose of protecting the nation’s borders. They cannot become general drug-search or other law enforcement efforts.
- However, these stops by Border Patrol agents are not remaining confined to that border security purpose. On the roads of California and elsewhere in the nation – places far removed from the actual border – agents are stopping, interrogating, and searching Americans on an everyday basis with absolutely no suspicion of wrongdoing.
Computer World reports:
- The bottom line is that the extraordinary authorities that the government possesses at the border are spilling into regular American streets.
Border agents don’t need probable cause and they don’t need a stinking warrant since they don’t need to prove any reasonable suspicion first. Nor, sadly, do two out of three people have First Amendment protection; it is as if DHS has voided those Constitutional amendments and protections they provide to nearly 200 million Americans.Wired pointed out in 2008 that the courts have routinely upheld such constitution-free zones:
***
Don’t be silly by thinking this means only if you are physically trying to cross the international border. As we saw when discussing the DEA using license plate readers and data-mining to track Americans movements, the U.S. “border” stretches out 100 miles beyond the true border. Godfather Politics added:
But wait, it gets even better! If you live anywhere in Connecticut, Delaware, Florida, Hawaii, Maine, Massachusetts, Michigan, New Hampshire, New Jersey or Rhode Island, DHS says the search zones encompass the entire state.Immigrations and Customs Enforcement (ICE) and Customs and Border Protection (CBP) have a “longstanding constitutional and statutory authority permitting suspicionless and warrantless searches of merchandise at the border and its functional equivalent.” This applies to electronic devices, according to the recent CLCR “Border Searches of Electronic Devices” executive summary [PDF]:
Fourth AmendmentThe ACLU said, Wait one darn minute! Hello, what happened to the Constitution? Where is the rest of CLCR report on the “policy of combing through and sometimes confiscating travelers’ laptops, cell phones, and other electronic devices—even when there is no suspicion of wrongdoing?” DHS maintains it is not violating our constitutional rights, so the ACLU said:
The overall authority to conduct border searches without suspicion or warrant is clear and longstanding, and courts have not treated searches of electronic devices any differently than searches of other objects. We conclude that CBP’s and ICE’s current border search policies comply with the Fourth Amendment. We also conclude that imposing a requirement that officers have reasonable suspicion in order to conduct a border search of an electronic device would be operationally harmful without concomitant civil rights/civil liberties benefits. However, we do think that recording more information about why searches are performed would help managers and leadership supervise the use of border search authority, and this is what we recommended; CBP has agreed and has implemented this change beginning in FY2012.***
If it’s true that our rights are safe and that DHS is doing all the things it needs to do to safeguard them, then why won’t it show us the results of its assessment? And why would it be legitimate to keep a report about the impact of a policy on the public’s rights hidden from the very public being affected?***
As Christian Post wrote, “Your constitutional rights have been repealed in ten states. No, this isn’t a joke. It is not exaggeration or hyperbole. If you are in ten states in the United States, your some of your rights guaranteed by the Bill of Rights have been made null and void.”
The ACLU filed a Freedom of Information Act request for the entire DHS report about suspicionless and warrantless “border” searches of electronic devices. ACLU attorney Catherine Crump said “We hope to establish that the Department of Homeland Security can’t simply assert that its practices are legitimate without showing us the evidence, and to make it clear that the government’s own analyses of how our fundamental rights apply to new technologies should be openly accessible to the public for review and debate.”
Meanwhile, the EFF has tips to protect yourself and your devices against border searches. If you think you know all about it, then you might try testing your knowledge with a defending privacy at the U.S. border quiz.
Federal agents at the border do not need any reason to search through travelers’ laptops, cell phones or digital cameras for evidence of crimes, a federal appeals court ruled Monday, extending the government’s power to look through belongings like suitcases at the border to electronics.Going further down the high tech Big Brother rabbit hole, the FBI wants a backdoor to all software. (Leading European computer publication Heise said in 1999 that the NSA had already built a backdoor into all Windows software.)
***
The 9th U.S. Circuit Court of Appeals sided with the government, finding that the so-called border exception to the Fourth Amendment’s prohibition on unreasonable searches applied not just to suitcases and papers, but also to electronics.
***
Travelers should be aware that anything on their mobile devices can be searched by government agents, who may also seize the devices and keep them for weeks or months. When in doubt, think about whether online storage or encryption might be tools you should use to prevent the feds from rummaging through your journal, your company’s confidential business plans or naked pictures of you and your-of-age partner in adult fun.
The CIA wants to spy on you through your dishwasher and other appliances.
And they’re probably bluffing and exaggerating, but the Department of Homeland Security claims they will soon be able to know your adrenaline level, what you ate for breakfast and what you’re thinking … from 164 feet away.
It has gotten so bad that even the mainstream media is sounding the alarm.
Big Corporations Are Spying On Us As Well
Big companies have been selling our data for years.
Bloomberg noted recently that big companies are giving data to the NSA and other government agencies … in return for favored treatment (and see this).
But spying by private companies is getting more and more intrusive.
For example, companies have developed billboards that can watch you. And see this.
Verizon has applied for a patent that would allow your television to track what you are doing, who you are with, what objects you’re holding, and what type of mood you’re in.
The Washington Times reports:
New technology would allow cable companies to peer directly into television watchers’ homes and monitor viewing habits and reactions to product advertisements.(And some folks could conceivably be spying on you through your tv using existing technology.)
The technology would come via the cable box, and at least one lawmaker on Capitol Hill is standing in opposition.
Mass. Democratic Rep. Michael Capuano has introduced a bill, the We Are Watching You Act, to prohibit the technology on boxes and collection of information absent consumer permission. The bill would also require companies that do use the data to show “we are watching you” messages on the screen and to explain just what kinds of information is being captured and for what reasons, AdWeek reported.
The technology includes cameras and microphones that are installed on DVRs or cable boxes and analyzes viewers’ responses, behaviors and statements to various ads — and then provides advertisements that are targeted to the particular household.
Specifically, the technology can monitor sleeping, eating, exercising, reading and more, AdWeek reported.
“This may sound preposterous, but it’s neither a joke nor an exaggeration,” said Mr. Capuano in a statement, AdWeek reported. “These DVRs would essentially observe consumers as they watch television as a way to super-target ads. It is an incredible invasion of privacy.”
And the new Xbox can spy on you as well.
Postscript: This is not some “post-9/11 reality”. Spying on Americans started before 9/11.
And the national security boys can choose to share U.S. civilian information with federal, state, local, or foreign entities for analysis of possible criminal behavior, even if there is no reason to suspect them.
And many say that the spying isn’t being done to keep us safe … but to crush dissent and to smear people who uncover unflattering this about the government … and to help the too big to fail businesses compete against smaller businesses (and here).
And for other reasons. For example, the Atlantic notes:
In 2008, NSA workers told ABC News that they routinely eavesdropped on phone sex between troops serving overseas and their loved ones in America.Note: Here’s a full report card on how well the government has been balancing civil liberties with other concerns.
Category: Legal, Think Tank, War/Defense
Government Spying: Why You Can't 'Just Trust Us'
For proof that the current surveillance programs are ripe for abuse, Americans need only look at what preceded them.
- by Marcy Wheeler
- June 19, 2013
Since we learned that the government has been collecting and storing Americans’ call data for years, Senate Intelligence Committee chair Dianne Feinstein; her counterpart in the House, Mike Rogers; and James Clapper, director of national intelligence, have been trying to claim it is not as bad as it sounds. The collection doesn’t include the content of communications, merely “metadata,” they argue, and anyway, the secret Foreign Intelligence Surveillance Act (FISA) court limits the circumstances under which the government can access this information. “The court only allows the data to be queried when there is a reasonable suspicion, based on specific facts, that the particular basis for the query is associated with a foreign terrorist organization,” says Clapper.
In other words, the government’s response amounts to “trust us.”
But Americans have good reason to distrust the program, which, according to The Washington Post, is called MAINWAY. That’s true not just because history reminds us that the government has abused surveillance authorizations in the past, as it did when it used COINTELPRO to spy on dissidents decades ago. It’s also true because one of the direct predecessors of this program proved ripe for abuse.
Beginning in 2002, the government worked with the three major phone companies (at the time AT&T, Verizon and MCI) to set up lines in the FBI’s New York office—and later its Washington counterterrorism office—from which phone company employees would be able to access their company’s databases directly. FBI agents would have those employees query the database right from the FBI office, mostly using National Security Letters (NSLs)—a means of obtaining information directly from service providers without review by a judge. The purpose was similar to the newly revealed collection program: to allow the government quick access to metadata on any calls made in the United States. The metadata was then uploaded and entered into government computers in an easily usable format.
The earlier program started being phased out in 2006, just as the current one was being phased in, suggesting that this program replaced the earlier one. By creating copies of phone company databases, which are updated daily, the government has simply shifted the companies’ role. Today, the phone companies turn everything over in bulk. Rather than having phone company employees access the data, the NSA or FBI does it.
A 2010 report by the Justice Department’s inspector general (IG) shows that the predecessor program was a mess. The FBI failed to keep adequate records of requests made by the government to phone companies, frequently violating the limits of what they were entitled to take. More troubling still is a tool the FBI implemented, ostensibly for emergency situations, called “exigent letters”: basically a request to phone companies to provide data immediately, with a promise to provide the appropriate legal paperwork—either an NSL or a subpoena—after the fact. Using exigent letters, the FBI obtained records for more than 3,000 phone numbers, often failing to submit the paperwork, or doing so without the appropriate approvals. Requests were often approved by junior staffers, who had no authority to do so.
Moreover, some requests were not tied, as required, to a specific authorized investigation. Significant numbers (perhaps 17 percent, judging from figures in the IG report) were tied not to national security investigations, but to domestic ones. At times, the FBI requested information on phone numbers when no investigation was pending. When accepting information from phone companies, the FBI didn’t always compare its contents with the original request and therefore may have entered unrelated information into FBI databases. In an unknown number of other requests, the FBI submitted no paperwork at all.
In addition, in several cases, the FBI obtained reporters’ phone records by using this method, including the Post’s Ellen Nakashima and the Times’s Jane Perlez.
These abuses were uncovered over a number of years. As early as November 2004, the phone companies started complaining that they didn’t have the proper paperwork, which they needed to prove they had not turned over their customers’ phone records illegally. Then, as the FBI tried to provide legal cover for the missing paperwork, more senior FBI figures became aware of the problems. The IG investigation—the early phases of which started not long after being mandated by the Patriot Act renewal in 2006—itself identified some problems. But it appears their full extent was not uncovered until the IG investigation discovered them in 2008—two years after the current practice had been put into place.
Based on the details revealed to date, the government has improved oversight in at least two ways. According to NSA chief Keith Alexander’s testimony at a congressional hearing on June 18, only twenty-two specially trained officials have the authority to make or approve queries. Previously, most analysts making queries had little experience with national security investigations or NSLs.
In addition, the government at least claims all queries are documented and can be audited, though it has provided no details on how it ensures documentation. Alexander testified that the executive branch reviews queries and provides details on those queries in aggregate to the FISA court and Congress. The Court does not—as Congressman Adam Schiff suggested ought to happen—review the queries themselves.
Several other potential oversight mechanisms have gotten weaker since 2006. Whistleblowers might still expose problems, but national security whistleblowers are not provided the same legal protections as whistleblowers in other areas of government. The inspector general is working on a review of the department’s use of NSLs and Section 215 orders (the latter being the Patriot Act provision currently being used). But it has been five years since the last review of the Section 215 programs, which assessed the program implementation only for 2006, and the discussion of this collection program appeared in a still-redacted classified appendix. Further, this new report will cover the program only through 2009. So even the most useful tools for exposing past abuses—a review of the actual queries by the Justice Department’s inspector general—is only now auditing how the program was implemented four years ago.
Perhaps most important, removing the phone companies from the search process eliminates one check on the process, because the companies no longer have the opportunity or incentive to do what they did almost a decade ago: demand paperwork to meet the terms of the law.
At the hearing on Capitol Hill, the NSA and the FBI tried to demonstrate the value of the government’s dragnet by pointing to terrorist plots it helped thwart. Witnesses boasted that ten plots have been foiled with its help over seven years—a rather unimpressive figure when one considers that these “plots” include things like indirect material support of terrorism, and that the government has thwarted five times that many plots just in the last three years. Does this truly require the government to collect all Americans’ phone data?
Please support our journalism. Get a digital subscription for just $9.50!
The hearing suggested that the answer is no. When Congressman Schiff asked witnesses whether the same information could have been obtained with individual requests to the phone companies for the data, they admitted that, with some work, they could (and now, with the exposure of the program, are considering doing just that).
The conclusion: for seven years, the government has been systematically collecting and keeping our phone records, all to thwart a handful of plots that, it turns out, could have been stopped in a much less invasive fashion. Is this really a program the Obama administration wants to defend?
Booz Allen, the World's Most Profitable Spy Organization
In 1940, a year before the attack on Pearl Harbor, the U.S. Navy began to think about what a war with Germany would look like. The admirals worried in particular about the Kriegsmarine’s fleet of U-boats, which were preying on Allied shipping and proving impossible to find, much less sink. Stymied, Secretary of the Navy Frank Knox turned to Booz, Fry, Allen & Hamilton, a consulting firm in Chicago whose best-known clients were Goodyear Tire & Rubber (GT) and Montgomery Ward. The firm had effectively invented management consulting, deploying whiz kids from top schools as analysts and acumen-for-hire to corporate clients. Working with the Navy’s own planners, Booz consultants developed a special sensor system that could track the U-boats’ brief-burst radio communications and helped design an attack strategy around it. With its aid, the Allies by war’s end had sunk or crippled most of the German submarine fleet.
- June 20, 2013
That project was the start of a long collaboration. As the Cold War set in, intensified, thawed, and was supplanted by global terrorism in the minds of national security strategists, the firm, now called Booz Allen Hamilton (BAH), focused more and more on government work. In 2008 it split off its less lucrative commercial consulting arm—under the name Booz & Co.—and became a pure government contractor, publicly traded and majority-owned by private equity firm Carlyle Group (CG). In the fiscal year ended in March 2013, Booz Allen Hamilton reported $5.76 billion in revenue, 99 percent of which came from government contracts, and $219 million in net income. Almost a quarter of its revenue—$1.3 billion—was from major U.S. intelligence agencies. Along with competitors such as Science Applications International Corp. (SAIC), CACI, and BAE Systems (BA/), the McLean (Va.)-based firm is a prime beneficiary of an explosion in government spending on intelligence contractors over the past decade. About 70 percent of the 2013 U.S. intelligence budget is contracted out, according to a Bloomberg Industries analysis; the Office of the Director of National Intelligence (ODNI) says almost a fifth of intelligence personnel work in the private sector.
It’s safe to say that most Americans, if they’d heard of Booz Allen at all, had no idea how huge a role it plays in the U.S. intelligence infrastructure. They do now. On June 9, a 29-year-old Booz Allen computer technician, Edward Snowden, revealed himself to be the source of news stories showing the extent of phone and Internet eavesdropping by the National Security Agency. Snowden leaked classified documents he loaded onto a thumb drive while working for Booz Allen at an NSA listening post in Hawaii, and he’s promised to leak many more. After fleeing to Hong Kong, he’s been in hiding. (He didn’t respond to a request for comment relayed by an intermediary.)
The attention has been bad for Booz Allen’s stock, which fell more than 4 percent the morning after Snowden went public and still hasn’t recovered. Senator Dianne Feinstein (D-Calif.), who chairs the Select Committee on Intelligence, has called for a reexamination of the role of private contractors in intelligence work and announced she’ll seek to restrict their access to classified information. Booz Allen declined to comment on Snowden beyond its initial public statement announcing his termination.
The firm has long kept a low profile—with the federal government as practically its sole client, there’s no need for publicity. It does little, if any, lobbying. Its ability to win contracts is ensured by the roster of intelligence community heavyweights who work there. The director of national intelligence, James Clapper—President Obama’s top intelligence adviser—is a former Booz Allen executive. The firm’s vice chairman, Mike McConnell, was President George W. Bush’s director of national intelligence and, before that, director of the NSA. Of Booz Allen’s 25,000 employees, 76 percent have classified clearances, and almost half have top-secret clearances. In a 2003 speech, Joan Dempsey, a former CIA deputy director, referred to Booz Allen as the “shadow IC” (for intelligence community) because of the profusion of “former secretaries of this and directors of that,” according to a 2008 book, Spies for Hire: The Secret World of Intelligence Outsourcing. Today Dempsey works for Booz Allen.
It’s possible that fallout from the Snowden revelations will lead to significant changes in intelligence contracting. The Senate intelligence committee has been pressuring spy agencies for years to reduce their reliance on contractors. And in the age of the sequester, even once untouchable line items such as defense and intelligence spending are vulnerable to cuts.
Yet conversations with current and former employees of Booz Allen and U.S. intelligence officials suggest that these contractors aren’t going anywhere soon. Even if Snowden ends up costing his former employer business, the work will probably just go to its rivals. Although Booz Allen and the rest of the shadow intelligence community arose as stopgap solutions—meant to buy time as shrunken, post-Cold War agencies tried to rebuild after Sept. 11—they’ve become the vine that supports the wall. As much as contractors such as Booz Allen have come to rely on the federal government, the government relies on them even more.
Edward Snowden was not hired as a spy. He’s a mostly self-taught computer technician who never completed high school, and his first intelligence job was as a security guard at an NSA facility. In an interview in the Guardian, he says he was hired by the Central Intelligence Agency for his computer skills to work on network security. In 2009 he left for the private sector, eventually ending up at Booz Allen. The job he did as a contractor for the NSA appears to have been basic tech support and troubleshooting. He was the IT guy.
People in intelligence tend to divide contract work into three tiers. In the first tier are the least sensitive and most menial jobs: cutting the grass at intelligence facilities, emptying the trash, sorting the mail. In classified facilities even the janitors need security clearances—the wastebaskets they’re emptying might contain national secrets. That makes these jobs particularly hard to fill, since most people with security clearances are almost by definition overqualified for janitorial work.
Snowden, with his computer expertise, fit in the middle tier: people with specialized skills. When the U.S. military first began ramping up its use of contractors during the Vietnam War, these jobs made up much of the hiring—the Pentagon was desperate for repairmen for its increasingly complex weapons and transport systems. Also in this tier are translators, interrogators, and investigators who handle background checks for government security clearances. Firms such as CSC (CSC) and L-3 Communications (LLL) specialize in this tier. Booz Allen competes for some of that work, but it tends to focus on the highest tier: big contracts that can involve everything from developing strategies to defeat al-Qaeda in the Islamic Maghreb to designing software systems to writing speeches for senior officials. Tier three contractors often are, for all intents and purposes, spies—and sometimes spymasters.
William Golden heads a recruiting and job placement company for intelligence professionals. In mid-June, he’s trying to fill three slots for contractors at the Defense Intelligence Agency. As it happens, Booz Allen isn’t involved, but these are the sort of jobs the firm has filled in thousands of other instances, Golden says. Two postings are for senior counter-intelligence analyst openings in Fort Devens, Mass., one focusing on the threat to federal installations in Massachusetts, the other on Southwest Asia. The contractors would be trawling through streams of intelligence, from digital intercepts and human sources alike, writing reports and briefings just like the DIA analysts they would be sitting next to. Both postings require top-secret clearances, and one would require extensive travel. The third job is for a senior linguist fluent in Malayalam, spoken mostly in the Indian state of Kerala, where there’s a growing Maoist insurgency. That the Pentagon is looking for someone who speaks the language suggests American intelligence assets are there. The listing specifies “austere conditions.”
Golden says he constantly sees openings at Booz Allen and other contractors for “collection managers” in posts around the world. “A collection manager is someone at the highest level of intelligence who decides what assets get used, how they get used, what goes where,” he says. “They provide thought, direction, and management. They basically have full status, as if they were a government employee. The only thing they can’t do is spend and approve money or hire and fire government workers.”
The pay fluctuates widely, depending on the candidates’ skills and experience. “This money comes from the intelligence budget, so there isn’t much oversight,” Golden says. He estimates that the Malayalam translator job, for example, will pay between $180,000 and $225,000 a year. That’s partly to compensate for the austere conditions as well as insurgents’ tendency, unmentioned in the posting, to target translators first. The pay is also a reflection that the past 10 years have been boom times for private spies.
The large-scale hiring of intelligence contractors can be traced directly to Sept. 11. The al-Qaeda attacks triggered a bipartisan chorus on Capitol Hill for more and better intelligence—and correspondingly massive increases in the federal budget to pay for it. There’s plenty of evidence that the effort has disrupted terrorist plots. It has also created a lot more contractor work. The intelligence community had been shrinking throughout the 1990s; with the Soviet Union gone, intelligence didn’t seem as important to politicians, and there were budget cuts and a wave of retirements at the CIA, NSA, and DIA. In late 2001 the only way to get enough experienced people to meet demand was with contractors, many of them the same experts the government had trained decades before and then let go. “We were able to expand very, very quickly by using contract personnel,” said Ronald Sanders, then ODNI’s associate director for human capital, in a 2008 call with reporters. “They were able to come in quickly and perform the mission even as we were busy recovering the IC’s military and civilian workforce.”
Contractors such as Booz Allen were seen as a temporary measure—surge capacity—to give the government time to hire and train its own employees. Michael Brown, a retired rear admiral, tells about trying to develop the Navy’s cyberwarfare programs in 2001. None of his personnel were cybersecurity experts, so he trained Navy linguists—traditionally considered some of the brainier sailors—for the job. “The Navy was able to use contractors to augment those trainees while it developed a permanent program,” Brown says. He himself now works for RSA Security (EMC), a Bedford (Mass.) cybersecurity company that does a lot of business with the government.
As the government intelligence workforce has grown, however, contractor head count hasn’t returned to pre-Sept. 11 levels. In the 2008 interview, Sanders said only 5 percent of contractors working for various intelligence agencies were for “surge requirements.” In a report published this March, the Senate intelligence committee complained that “some elements of the IC have been hiring additional contractors after they have converted or otherwise removed other contractors, resulting in an overall workforce that continues to grow.” The ODNI’s public affairs office disputes this, saying “core contractor personnel” has been cut by 36 percent since 2007.
Proponents of intelligence contracting say there are good reasons private firms have become a permanent part of the landscape. Not every task requires a full-time federal employee. Building a classified facility or a new database is a short-term project that’s ideal for contract labor—the job takes a few months or a couple years, and it doesn’t make sense to hire and train new employees just for that. In theory, contract labor is cheaper, since the government isn’t on the hook for the worker’s salary after the job is over, much less his health care or pension. For the military, it’s often the only way to get additional work done without violating the caps on manpower written into legislation. And it’s abetted by the dysfunctional funding environment in Washington, where money even for long-term projects is increasingly appropriated in year-to-year emergency supplemental spending bills, creating a sense of uncertainty that makes it harder to hire permanent employees.
Senior intelligence officials also say contractors are a pipeline to innovation in the private sector. The contemporary version of Q’s laboratory—that storied incubator for James Bond’s spy toys—is Silicon Valley, where startups are developing technology that can discern patterns and connections in oceans of raw data, among other feats of computer science. In an interview with Bloomberg Businessweek, Vice Chairman McConnell points out that while Booz Allen is well-known for hiring former spies like himself, the company also recruits heavily from tech. A 2008 study by the ODNI reported that 56 percent of intelligence contractors provided unique expertise not found among government intelligence officers.
“As DNI, I absolutely wanted the lift and creativity and the power of the private sector,” says McConnell, using the initials for his old job. “Because I’d become irrelevant if I didn’t stay in tune with technology and its evolution. The most innovative, creative, dominant country in the world is the United States, and it’s mostly because of the efficiency of the free market.” Some intelligence contractors, such as Palo Alto (Calif.)-based Palantir Technologies, have gone so far as to locate in commercial tech hubs rather than the traditional intelligence corridor that stretches 50 miles from Reston, Va., to the Fort Meade (Md.) headquarters of the NSA.
Even so, spending can spin way out of control. According to the ODNI, a typical contractor employee costs $207,000 a year, while a government counterpart costs $125,000, including benefits and pension. One of the most notorious projects was the NSA’s Trailblazer. Intended as an advanced program to sort and analyze the vast volume of phone and Web traffic that the NSA collects hourly, Trailblazer was originally set to cost $280 million and take 26 months. Booz Allen was part of a five-company consortium working on the project. (SAIC was the lead contractor.) “In Trailblazer, NSA is capturing the best of industry technology and experience to further their mission,” Booz Allen Vice President Marty Hill said in a 2002 press release. In 2006, when the program shut down, it had failed to meet any of its goals, and its cost had run into the billions of dollars. An NSA inspector general report found “excessive labor rates for contractor personnel,” without naming the contractors. Several NSA employees who denounced the waste were fired; one, a senior executive named Thomas Andrews Drake, was charged under the Espionage Act after he spoke to a reporter. (The charges were eventually dropped.)
A U.S. Department of Homeland Security computer systems contract awarded to Booz Allen around the same time had similar issues. Over the course of three years, costs exploded from the original $2 million to $124 million, in large part, auditors at the Government Accountability Office would later report, because of poor planning and oversight. But even when the problems came to light, as the Washington Post reported, DHS continued to renew the contract and even give Booz Allen new ones, because the agency determined it couldn’t build, or even run, the system on its own.
Booz Allen spokesman James Fisher and NSA spokeswoman Vaneé Vines both declined to comment on Trailblazer. (Former NSA Director Michael Hayden has since said publicly that the project failed because the spy agency’s plan for it was unrealistic.) Fisher also declined to comment on the DHS contract; Peter Boogaard, a spokesman for that agency, did not immediately return a call for comment.
Booz Allen and its competitors are able to keep landing contracts and keep growing, critics charge, not because their expertise is irreplaceable but because their Rolodexes are. Name a retired senior official from the NSA or the CIA or the various military intelligence branches, and there’s a good chance he works for a contractor—most likely Booz Allen. Name a senior intelligence official serving in the government, and there’s a good chance he used to work for Booz Allen. (ODNI’s Sanders, who made the case for contractors, is now a vice president at the firm, which declined to make him available for an interview.) McConnell and others at Booz Allen are quick to point out that the contracting process has safeguards and oversight built in and that it has matured since the frenzied years just after Sept. 11. At the same time, the firm’s tendency to scoop up—and lavishly pay—high-ranking intelligence officers once they retire suggests the value it places on their address books and in having their successors inside government consider Booz Allen as part of their own retirement plans.
Rich contractor salaries create a classic public-private revolving door. They pull people from government intelligence, deplete the ranks, and put more experience and knowledge in the private sector, which makes contractors even more vital to the government. “Now you go into government for two or three years, get a clearance, and migrate to one of the high-paying contractors,” says Steven Aftergood, who heads the Project on Government Secrecy at the Federation of American Scientists. That’s what Snowden did. “You have to have a well-developed sense of patriotism to turn that money down,” Aftergood says.
As a result, says Golden, the headhunter, a common complaint in spy agencies is that “the damn contractors know more than we do.” That could have been a factor in the Snowden leak—his computer proficiency may have allowed him to access information he shouldn’t have been allowed to see. Snowden is an anomaly, though. What he did with that information—copying it, getting it to the press, and publicly identifying himself as the leaker—cost him his job and potentially his freedom, all for what appear so far to be idealistic motives. The more common temptation would be to use knowledge, legally and perhaps not even consciously, to generate more business.
In the wake of the Snowden leak, Congress is paying more attention to contractors like Booz Allen and the role they play in intelligence gathering. Lawmakers on both sides of the aisle say that the ease with which Snowden was able to gain access to and divulge classified information highlights the need for greater oversight of contractors’ activities. “I’m just stunned that an individual who did not even have a high school diploma, who did not successfully complete his military service, and who is only age 29 had access to some of the most highly classified information in our government,” Senator Susan Collins (R-Me.) told reporters on Capitol Hill on June 11. “That’s astonishing to me, and it suggests real problems with the vetting process. The rules are not being applied well or they need to be more strict.”
Changing them, however, may be easier said than done. “At the very highest level, whether at the White House or the Pentagon, there will always be a contractor in the room,” says Golden. “And the powers that be will turn around and say, ‘That’s a brilliant plan, how do we make that work?’ And a contractor will say, ‘I can do that.’ ”

In Depth Review: New NSA Documents Expose How Americans Can Be Spied on Without A Warrant
June 21, 2013 | By Kurt Opsahl and Trevor Timm
The Guardian published a new batch of secret leaked FISA court and NSA documents yesterday, which detail the particulars of how government has been accessing Americans’ emails without a warrant, in violation of the Constitution. The documents lay bare fundamental problems with the ineffectual attempts to place meaningful limitations on the NSA’s massive surveillance program.
Essentially, the new documents, dated July 2009 and approved in August 2010, detail how the NSA deals with the huge streams of information it receives during the collection program that gathers the content of email and telephone calls, allowing it to keep vast quantities of content it could never get with a warrant. They may not be the current procedures - more on that in another blog post shortly.
The Guardian published two documents: one showing the procedures for determining if their target is foreign for purposes of surveillance under the FISA Amendments Act (FAA) and the other describing the NSA’s “minimization” procedures when they come across United States persons, which also sets out the myriad ways they can keep Americans’ communications instead of minimizing them.
Weak Standards for Avoiding Intentionally Targeting Americans
The FAA was enacted in 2008, intending to put a veneer of legal restrictions on aspects of the unconstitutional NSA spying program that has been in place since 2001. The heavily criticized law purports to protect Americans by prohibiting the NSA from “intentionally targeting” United States persons. The procedures describe a process more intent on making sure it was not “intentional” than ensuring Americans were not actually spied upon.
The Washington Post previously reported that the NSA only needs to have 51% confidence in a person’s “foreignness.” These new documents reveal that if the NSA cannot determine its target's 'foreignness,' they can keep on spying. Instead, you “will be presumed to be a non-United States person unless [you] can be positively identified as a United States person."
The targeting document also references a key fact that the NSA has previously shrouded in secrecy and word games: the existence of an NSA database of the content of communications. When checking for “foreignness,” the document instructs the NSA to “Review NSA content repositories and Internet communications data repositories.” In the Jewel litigation, we have contended for years that the NSA has a database of content, and now have an explicit reference.
The targeting document also exposes the government’s deceptive strategy to down-play their gigantic database of all the phone call records of Americans, obtained by misusing Section 215 of the PATRIOT Act. They collect all information on who you call and how long the call lasts, but as President Obama emphatically stated "There are no names." Maybe not in that database, but the documents here shows that NSA also maintains a separate database of names, telephone numbers and other identifiers.
Minimizing Domestic Communications Rules Littered With Exceptions
The second document published yesterday explains the NSA’s “minimization” procedures. Minimization refers to the process that is supposed to limit the exposure of Americans. The NSA, however, has decided to minimize the minimization.
Critically, this document reveals various loopholes that allow the NSA to access your data and read your emails without a warrant. According to the NSA document, they can retain and use information from Americans if:
- They were retained due to limitation on the NSA’s ability to filter communications.
- They contain information on criminal activity or a threat of harm to people or property. This is not very comforting – the Fourth Amendment wouldn’t mean anything if the government could search your house everyday, but would only act if they found evidence of a crime inside.
- They are encrypted or could be used for traffic analysis.
Your protection is summed up best by the NSA’s own description: “Personnel will use reasonable discretion in determining whether information acquired must be minimized.” While the government claims that a court order is required before they listen to an American’s call, this is only if an analyst, in his reasonable discretion, decided that the parties were American. Otherwise, no court order and no Constitutional protections are applied.
- They contain "foreign intelligence information," including if it is contained within attorney-client communications.
Moreover, the minimization document has tremendous loopholes. The NSA may provide un-minimized data to the CIA and FBI, if they identify the target, and to foreign governments for “technical or linguistic assistance.” While the data would then be subject to rules for those agencies, there is little assurance there would be no abuse.
Using Email Encryption or Tor Is Grounds for Surveillance
At EFF, we have long recommended anyone who cares about privacy should use tools such as PGP (“Pretty Good Privacy”) email encryption and Tor, which anonymizes your location. We still do, but are disturbed by the way the NSA treats such communications.
In the United States, it has long been held that there is a Constitutional right to anonymous speech, and exercising this right cannot be grounds for the government to invade your privacy. The NSA blows by all that by determining that, if the person is anonymous, then necessarily the NSA is not intentionally targeting a US person, with a rare exception when they have "positively identified" the user as an American. Thus, in the NSA’s view, if you use Tor, the protections for a US person simply do not apply.
More appallingly, the NSA is allowed to hold onto communications solely because you use encryption. Whether the communication is domestic or foreign, the NSA will hang on to the encrypted message forever, or at least until it is decrypted. And then at least five more years.1
Traffic Analysis
NSA also says they can keep domestic communications that are "reasonably believed to contain technical data base information." The phrase “technical data base” is a specifically defined term that means “information maintained for cryptographic, traffic analytic or signal exploitation purposes.”
This suggests that the NSA believe it can keep domestic communication to the extent that they can be used for traffic analysis. This is a limitation without a meaning: all communications can be used for traffic analysis. In other words, with an aggressive read of this, they can keep all communications and don’t have to discard any.
Attorney-Client Privilege Means Nothing
The attorney client privilege is a long-standing feature of American law, one of the oldest and most cherished privileges through out the ages. As one court explained, it is the cornerstone of the privilege is “that one who seeks advice or aid from a lawyer should be completely free of any fear that his secrets will be uncovered.”
The NSA document shows they cut through this privilege like a hot knife through butter. The NSA only has to stop looking at the communication if the person is known to be under criminal indictment in the United States and communicating with her attorney for that particular matter.
This remarkably myopic view of the privilege means communications between attorneys and clients in many cases will be unduly spied on. This is exactly what the ACLU was worried about when they challenged the constitutionality of the FISA Amendments Act. They alleged that attorneys working with clients overseas had an ethical obligation not to electronically communicate with them because the NSA was likely able to read their emails. While the Supreme Court dismissed their suit for lack of standing, these documents at least in part, confirm their fears.
This could also mean any attorney-client communications with someone like Julian Assange of WikiLeaks, who has never been publicly acknowledged as indicted in the U.S., would be fair game.
Even where the privilege applies, the NSA does not destroy the information. The privileged nature is noted in the log, to “protect it” from use in criminal prosecutions, but the NSA is free to retain and use the information for other purposes. No limits on other uses, so long as the NSA General Counsel approves. This is a complete perversion of the attorney-client privilege. The privilege is designed to allow free communication of attorneys and those who they represent, so the client can get good counsel without hiding the truth from his attorney. It is not simply about preventing that communication from being used as evidence in a criminal case.
What It All Means: All Your Communications are Belong to U.S.
In sum, if you use encryption they’ll keep your data forever. If you use Tor, they’ll keep your data for at least five years. If an American talks with someone outside the US, they’ll keep your data for five years. If you’re talking to your attorney, you don’t have any sense of privacy. And the NSA can hand over you information to the FBI for evidence of any crime, not just terrorism. All without a warrant or even a specific FISA order.
It’s time the government is held accountable for these gross constitutional violations. Email your representative to demand a full-scale independent investigation into the NSA now.
While discussing the news this Sunday that NSA leaker Edward Snowden has now fled Hong Kong and is heading for Venezuela with the help of WikiLeaks and the Obama administrations extremely aggressive treatment of whistleblowers, The Guardian columnist Glenn Greenwald let Meet the Press host David Gregory have it when he asked Greenwald if we ought to be prosecuting journalists such as himself for publishing these leaks.
GREGORY: To the extent that you have aided and abetted Snowden, even in his current movement, why shouldn't you, Mr. Greenwald be charged with a crime?Greenwald reacted to the question by Gregory on Twitter as well this Sunday.
GREENWALD: I think it's pretty extraordinary that anybody who would call themselves a journalist would publicly muse about whether or not other journalist should be charged with felonies. The assumption in your question David is completely without evidence – the idea that I've aided and abetted him in any way.
The scandal that arose in Washington before our stories began was about the fact that the Obama administration is trying to criminalize investigative journalism by going through the emails and phone records of AP reporters, accusing a Fox News journalist of the theory that you just embraced, being a co-conspirator in felonies for working with sources. If you want to embrace that theory that every investigative journalist in the United States who work with their sources, who receive classified information is a criminal, and it's precisely those theories and precisely that climate that has become so menacing in the United States.
It's why The New Yorker's Jane Mayer said investigative reporting has come to a standstill, her word, as a result of the theory that you just referenced.
GREGORY: Well the question of who's a journalist may be up to a debate with regard to what you are doing. Of course, anybody who's watching this understands I was asking a question, and that question has been raised by lawmakers as well. I'm not embracing anything, but obviously, I take your point.

Nice, now we can add foreign relations to the ever expanding list of epic Obama failures.
